Russian hackers are shifting their interest to the cloud, and have successfully breached cloud infrastructure. This is what a joint advisory issued by the U.K.’s National Cyber Security Centre (NCSC), the NSA, CISA, the FBI, and cybersecurity agencies from Australia, Canada, and New Zealand (also known as “The Five Eyes”)
The advisory details recent tactics, techniques and procedures (TTPs) of the Russian hacking group known as APT29 (also known as Midnight Blizzard, the Dukes or Cozy Bear), which is associated with the Russian SVR.
Until recently, Russian Foreign Intelligence Service (SVR) cyber actors have targeted government entities, healthcare organizations, think tanks and energy facilities, mainly to obtain highly sensitive information for intelligence purposes. But now, these SVR actors are expanding their reach to include aviation, education, law enforcement, local and state councils, government financial departments and military organizations.
The most notable attacks carried our by these groups is the supply chain attack compromising software company SolarWinds and a campaign that targeted organizations developing the COVID-19 vaccine.
APT29 has been around since 2008, and have evolved from hacking on-premise networks to supply chain attacks and now exploiting cloud services themselves.
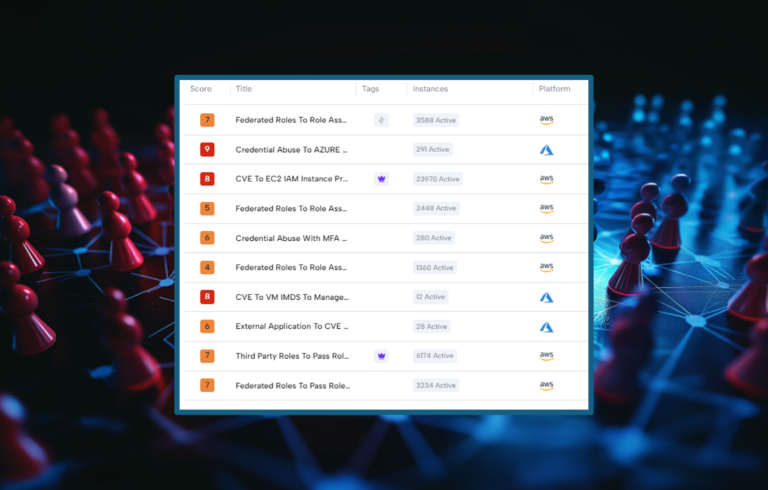
The report outlines several TTPs used by APT29 to gain initial access to cloud environments, including:
Access via service and dormant accounts
The attack group has leveraged brute force and password spraying to access service accounts which are typically used to run and manage applications and services and are often also highly privileged, hence gaining access to such accounts provides attackers with privileged initial access to the victim network, enabling them to launch further operations. In addition, SVR campaigns have also targeted dormant accounts (belonging to users who no longer work at the organization) but whose accounts remain operational.
Using Cloud-based token authentication to bypass credentials
Access to cloud-based user accounts is typically authenticated by credentials (username and password ) or system-issued access tokens. SVR actors has been using tokens to access their victims’ accounts, without needing a password .
Enrolling new devices to the cloud
The SVR has sometimes managed to bypass password authentication on personal accounts using password spraying and credential reuse, and sometimes using ‘MFA bombing’ (also known as: ‘MFA fatigue’), a technique in which the attacker repeatedly push Multi-factor Authentication requests to a victim’s device until the victim accepts the notification. Then the attacker registers it’s own device as a new device on the cloud tenant and gains access to the network.
Attack mitigation and identification
As for mitigation advice, the report includes the following best practices for system configuration:
- Using multi-factor authentication (MFA)
- Implementing strong password policies
- Disabling inactive accounts
- Implementing least privilege for service accounts
- Configuring device enrollment policies
In addition, the report suggests to actively monitor suspicious activities, including monitoring a variety of information sources (such as application events and host-based logs).
Conclusion:
The SVR is a sophisticated, capable threat actor. It is now focusing its efforts on cloud infrastructure as well as more traditional breach methods. To quote the report: “For organizations that have moved to cloud infrastructure, a first line of defense against an actor such as SVR should be to protect against SVR’s TTPs for initial access. Once the SVR gain initial access, the actor is capable of deploying highly sophisticated post compromise capabilities”.
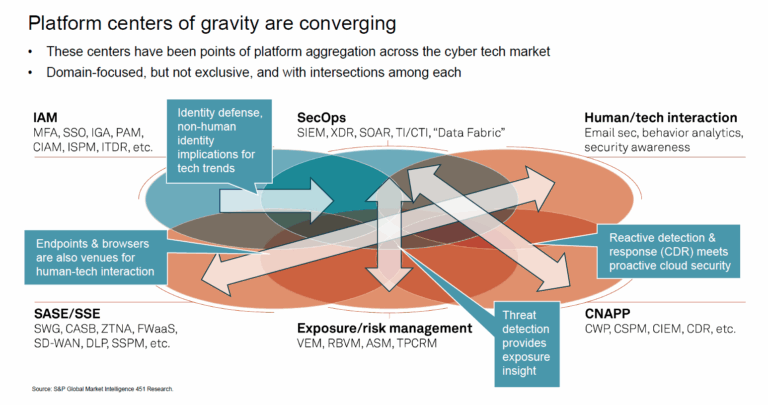
This means that in order to mitigate SVR-level attackers, organizations must improve their cloud security posture, their cloud red-teaming AND their real-time detection capabilities.