Table of Contents
This blog is a summary of our panel webinar, Eliminate Alert Overload: How to Achieve True Cloud Risk Reduction.
The Cloud Security Crisis No One Is Talking About Loudly Enough
Ask any CISO what keeps them up at night and the answer is rarely “we don’t have enough security tools.” More often, it is the opposite: too many tools, too many alerts, and too little clarity about where the real danger lies. That was the central theme of a recent Skyhawk Security webinar, where a panel of practitioners and industry experts came together to discuss one of the most pressing, and underappreciated, challenges in modern cloud security: alert overload and the urgent need to shift from reactive to preemptive defense.
The conversation was candid, practical, and grounded in real-world experience. What emerged was a clear picture of an industry at an inflection point, one where the old model of “scan, score, and hope for the best” is no longer sufficient, and where the organizations that will come out ahead are those that learn to distinguish genuine, weaponized risk from the noise that surrounds it.
The Threat Landscape has Dramatically Changed
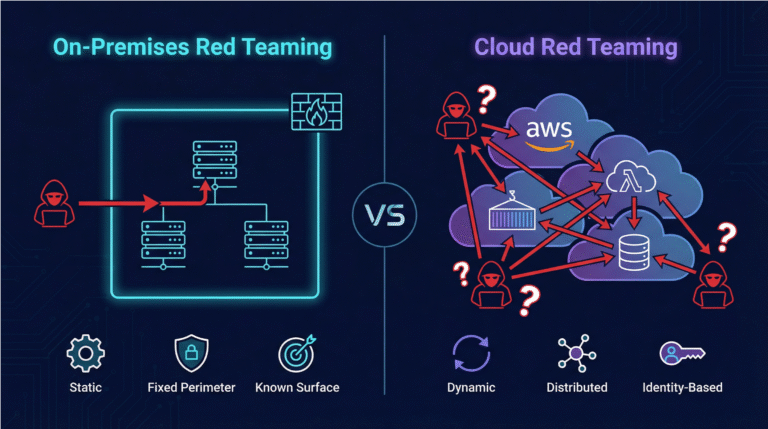
Rob Strechay, a principal analyst with more than 30 years of experience advising security and technology leaders, opened the discussion
with a frank assessment of where cloud security stands today. The field, he argued, has become almost unrecognizably complex compared to just a few years
ago.
“When you look at the entire field and where you have to go and secure yourself and your company, it is immensely tougher than it has ever been.” Amit Levran, CISO, Sunday Sky
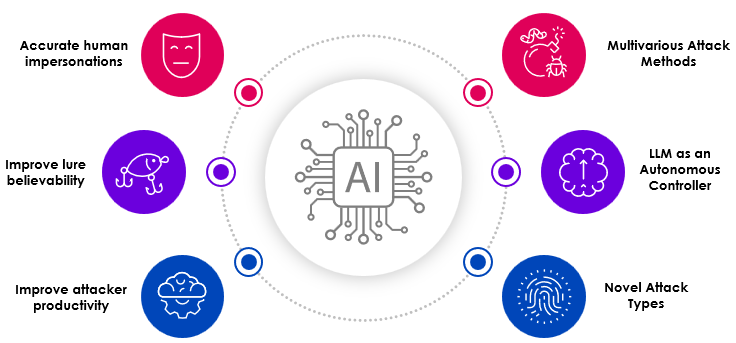
Several converging forces are driving this complexity. AI has fundamentally changed the economics of attacking: adversaries can now find vulnerabilities faster, craft more convincing attacks, and execute reconnaissance at a scale and speed that no human team can match. At the same time, the attack surface itself has expanded dramatically. Open-source dependencies now make up more than 75% of modern code bases, and 70% of security issues originate at the code stage, yet only 29% of developers run security scans locally. Security risk, in other words, begins at the keyboard, long before code ever reaches production.
The multi-cloud reality compounds the challenge further. Most organizations today operate across multiple cloud providers, AWS, Azure, Google Cloud, and others, each with its own security model, its own language, and its own attack vectors. Even organizations that believe they are single-cloud often discover that the boundaries between development and production environments are far more porous than they realized. As Amit Levran, Head of Security at SundaySky, pointed out: a development account that can assume a role on a production account effectively collapses the separation between the two environments, regardless of how they are labeled.
Regulatory pressure is adding yet another layer of complexity. The EU Cyber Resiliency Act, emerging AI governance frameworks, and a growing patchwork of compliance requirements are putting real teeth behind security obligations, and creating accountability that extends well beyond the security team itself.
The Alert Overload Problem: When More Information Means Less Clarity
Perhaps the most vivid moment of the webinar came when the panel discussed the sheer volume of alerts and findings that modern cloud security tools generate. Amit Levran described the experience that every security practitioner will recognize: opening a CNAPP dashboard for the first time and being confronted with tens of thousands, sometimes hundreds of thousands, of vulnerabilities, each assigned a severity score, with no clear guidance on where to begin.
“I was looking at the crazy number and saying, ‘Okay, what now?’ You have this huge list and there’s a severity assigned to each one, but does the severity really matter or does the exposure matter? If it’s a high severity and it can’t be weaponized against you, where do you prioritize it?”
Jennifer Gill, VP of Marketing at Skyhawk, added a striking data point from a recent industry event: a prospect at AWS re:Invent had just installed their CNAPP and discovered they had eight figures, tens of millions, of alerts. They had no idea where to start.
The problem with severity scores, as the panel made clear, is that they measure the theoretical risk of a vulnerability in isolation, not the actual risk it poses in the context of a specific environment. A critical vulnerability on an EC2 instance that has no path to sensitive data may be far less dangerous than a medium-severity finding on a machine that has direct access to crown jewels. The severity score does not tell you that. And in the age of AI-assisted exploitation, the window between a vulnerability being discovered and being weaponized has shrunk dramatically, meaning the cost of prioritizing the wrong things has never been higher.
Chen Burshan, CEO of Skyhawk Security, framed the challenge precisely:
“They don’t feel that they need more alerts. They need to be able to make sense of these alerts and understand which ones to handle first. They need to know which risks are actually weaponized and risking their environment.”
The Three Pillars of Effective Cloud Security
Drawing on his experience, Amit Levran outlined what he described as the three fundamental challenges that security teams are working to solve, using the analogy of protecting a house.
First: Map your exposure. Before you can defend anything, you need to know where an attack can come from. This means understanding every external exposure point, the doors, the windows, and yes, the garage door with the code set to 000000. Mapping vulnerabilities in those components is the essential starting point. Without it, prioritization is impossible.
Second: Prioritize what actually matters. Once you have a map, the question becomes: which vulnerabilities represent real, exploitable risk in your specific environment? Not theoretical risk based on a CVSS score, but actual risk, the vulnerabilities that an adversary could weaponize against your crown jewels today. This is where most tools fall short, and where the gap between “finding” and “risk” becomes most consequential.
Third: Build a real alarm system. When defenses fail, and eventually, they will, you need to know about it immediately, accurately, and with enough context to act. Not a simple rule-based alert that fires when a predefined condition is met, but a behavioral system that recognizes when something is out of the ordinary: a user accessing systems from an unexpected geography, an automated process invoking an assume-role action 50 times in three minutes, a pattern of behavior that no individual alert would flag but that collectively signals malicious intent.
How Skyhawk Security Addresses the Problem
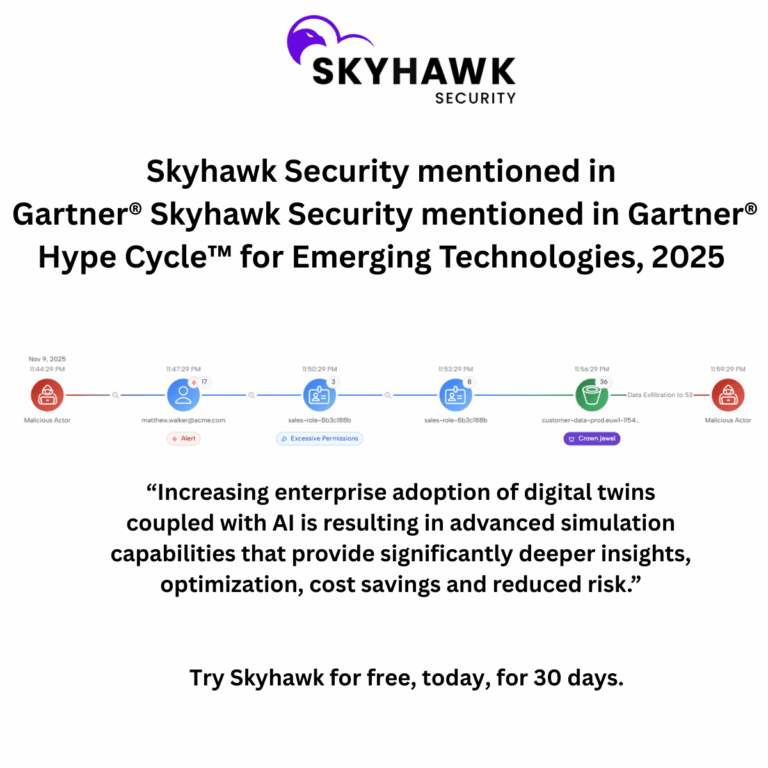
Chen Burshan provided an overview of how Skyhawk Security has evolved to address these challenges, and why the company’s approach differs fundamentally from traditional cloud security tools.
Skyhawk began with real-time threat detection and cloud observability: the ability to look across multiple events and behaviors, correlate them into a coherent picture of malicious intent, and surface a single, contextualized alert rather than a flood of individual findings. This addressed the “right of boom” problem — helping security teams respond more effectively when something goes wrong.
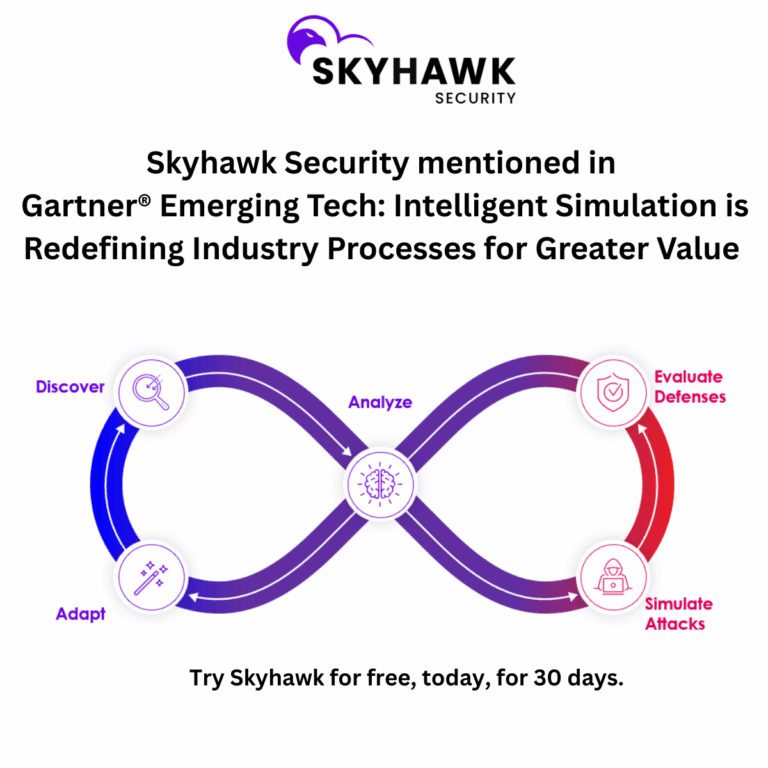
But the team recognized that detection alone is inherently reactive. No matter how good your detection capabilities are, you are always responding to something that has already happened. The question Skyhawk asked was: what if you could prepare your defenses before the attack, rather than after?
The answer was the Autonomous Purple Team, an AI-powered simulation engine that takes an adversarial view of a customer’s cloud environment, continuously testing security controls the way a real attacker would. Critically, this simulation runs entirely within Skyhawk’s SaaS platform using digital twin technology, a copy of the customer’s environment built using AI, with no impact on production systems and no disruption to operations.
“We make a copy of your environment using AI, but we do that within our SaaS platform. So there’s nothing disruptive to your environment. There’s no impact to you.”
The results have been consistent and striking. Across multiple customers and multiple CNAPP platforms, whether cloud-native tools or third-party systems, Skyhawk’s customers are achieving 99% or greater noise reduction. Amit Levran’s experience at SundaySky is illustrative: of all the alerts generated by his CNAPP, the number that Skyhawk validates as truly weaponizable in his specific environment is 0.3%. Not 1%. Not 5%. Zero point three percent.
That figure reframes the entire challenge. The question is not “how do I manage 100,000 alerts?” It is “how do I find the 300 that actually matter?” and then, within those, “which three do I work on today, which 20 do I work on this week, and which 100 do I work on this month?”
Industry Best Practices: What Security Leaders Should Do Now
Rob Strechay closed the panel with five recommendations for security leaders navigating this environment, a framework he acknowledged was really five answers to a question that asked for one.
Embed security, don’t bolt it on. Security needs to be part of the planning process from the beginning, not added as an afterthought. This is especially true as organizations build out AI systems, where the attack surface extends into training data, model inputs, and inference pipelines in ways that traditional security frameworks were not designed to address.
Replace manual review with automation. The volume of information that modern cloud environments generate is simply beyond human capacity to process manually. Automation is not a nice-to-have, it is a prerequisite for functioning at scale.
Shift policy from documentation to code. Security policies that live in documents are not enforced. Policies that live in code are. This shift is essential for maintaining consistent security posture across complex, multi-cloud environments.
Make supply chain transparency mandatory. Understanding your full attack surface means understanding not just your own code, but the open-source dependencies, upstream providers, and third-party integrations that make up your environment. Supply chain attacks are a growing vector, and visibility into that surface is foundational.
Make runtime protection continuous and behavioral. Rule-based monitoring catches what you know to look for. Behavioral monitoring catches what you don’t. The most dangerous intrusions, the ones that use valid credentials, legitimate access paths, and authorized tools — will never trigger a predefined rule. They will only be visible to a system that understands what normal looks like and flags what doesn’t fit.
The Bottom Line
The webinar closed with a memorable observation from Amit Levran, drawn from an unlikely source:
“No matter how fast you run, you will never run faster than the car. So it doesn’t matter how much time and effort you put into it, you will never be able to close all the vulnerabilities. Focus on the ones that are important.”
This is the essential insight of the preemptive security model: the goal is not to eliminate all risk, that is impossible. The goal is to understand which risks are real, which are weaponizable, and which represent the most direct path to your most critical assets. Everything else is noise.
For security teams drowning in alerts, struggling with prioritization, and facing a threat landscape that is growing more complex by the day, the path forward is not more tools or more alerts. It is the ability to see your environment through an attacker’s eyes, and to act on what you see before the attacker does.