Organizations are overwhelmed with CVEs that need to be examined, triaged, and if deemed a threat, remediated. Our customers tell us they have tens of thousands of vulnerabilities floated by various vendors that require significant analysis, which requires significant time and effort. The challenge is that teams do not have enough people and/or time to resolve that many alerts in a timely fashion. Security teams need a better way to prioritize these vulnerabilities then remediate only those that matter, a concept known as UVM, Unified Vulnerabilities Management.
The challenge with current UVM approaches is that they fall short in two ways:
- They analyze exploitability, not contextual weaponization.
- They do not analyze contextual detection capabilities as they relate to vulnerability. As a result, two exploitable vulnerabilities can both be classified as critical, while in wider, purple team-powered context, they do not present the same risk based on the ability to detect and therefore, block an active exploit.
The Benefits of Purple Team-Powered Tabletop Exercises
Purple Team-Powered Tabletop exercises include both red teams and blue teams and deliver a more comprehensive cybersecurity validation approach. The primary goal of these exercises is to reduce risk and identify gaps. The key metrics are as follows:
- Number and severity of true weaponized risks Identified: The number of true weaponized risks discovered in your existing cloud footprint. These findings can be the starting point of your red team to efficiently prepare for the tabletop exercise.
- Severity of Gaps: Not all gaps are equal. Classify the discovered gaps (e.g., critical, high, medium, low) to prioritize remediation efforts. The value of the exercise is demonstrated by the discovery and remediation of high-severity vulnerabilities.
- Detection and response: In cases when the vulnerability cannot be remediated, ensure your organization is ready to respond to the risk, in real time, to prevent the incident from becoming a breach.
- Action Item Completion Rate: After the exercise, a list of action items should be created to address the identified gaps. A high completion rate of these action items is a powerful metric that shows the exercise led to concrete improvements. The completion can be presented in two ways – actual remediation, or updated detections to indicate when a
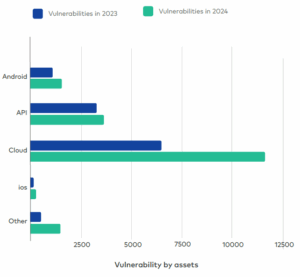
Cloud security teams are seeing an explosion of vulnerabilities. This makes sense as the cloud is required to be accessible to ensure productivity. It cannot be completely locked down, making it a target for threat actors. Cloud security teams need to leverage red teaming and tabletop exercises to understand which vulnerabilities present a true risk and then require remediation. If they cannot be remediated, the tabletop exercise can be used to improve detections and the security response should a known, unpatchable vulnerability be accessed by a threat actor.
Emerging Trends in the Threat Landscape
Figure 1: Shows the year-over-year change in vulnerability growth, with the largest increase in cloud vulnerabilities.(1)
Now, vulnerabilities and exposure do not always translate to risk, but we can see here that the number of vulnerabilities is increasing and there are more across every severity category. As organizations scale without prioritizing security, we see organizations are increasingly exposed. A recent Crowdstrike report shows a 136% increase in cloud intrusion in the first half of 2025 compared to all of 2025. They also found a 220% year-over-year increase in infiltrations that bypassed traditional defenses.
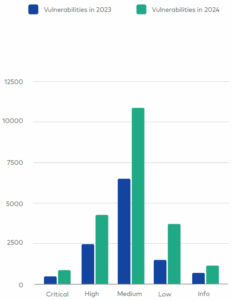
The Severity Factor of Vulnerabilities
Figure 2: Shows an 83% surge in critical vulnerabilities showing attackers are becoming more precise, opportunistic, and damaging. (2)
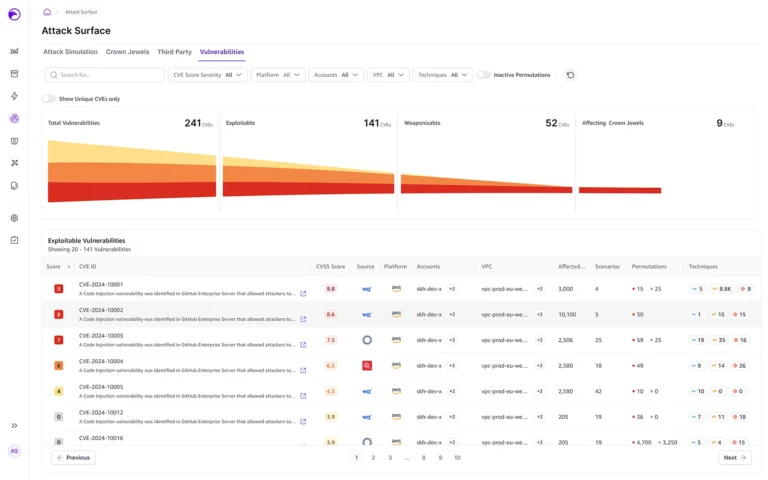
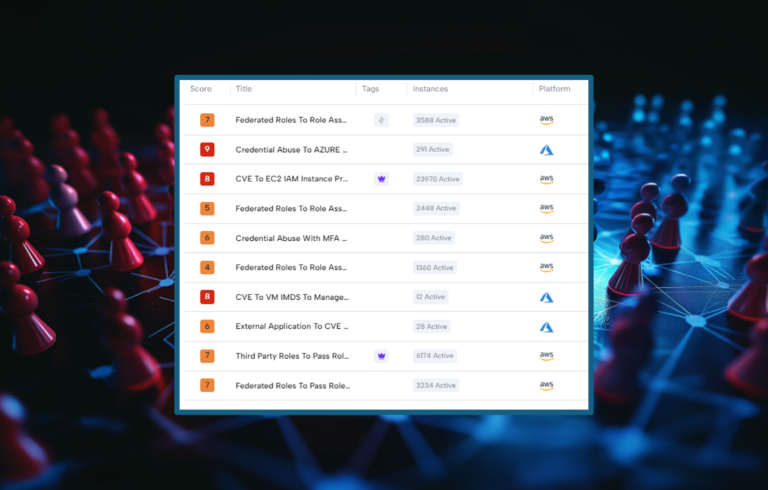
CNAPP platforms and other tools are surfacing tens of thousands of alerts and findings. Security teams must then triage these findings and determine if they are a threat or not. There are so many findings that security teams need a way to prioritize these findings to determine which are actual threats. Platforms offer internal severity scoring, but this is not enough. Security teams need to know what the risk is of the vulnerability being exploited.
Continuous AI-based Purple Team and Tabletop Exercises are Critical for Cloud Security
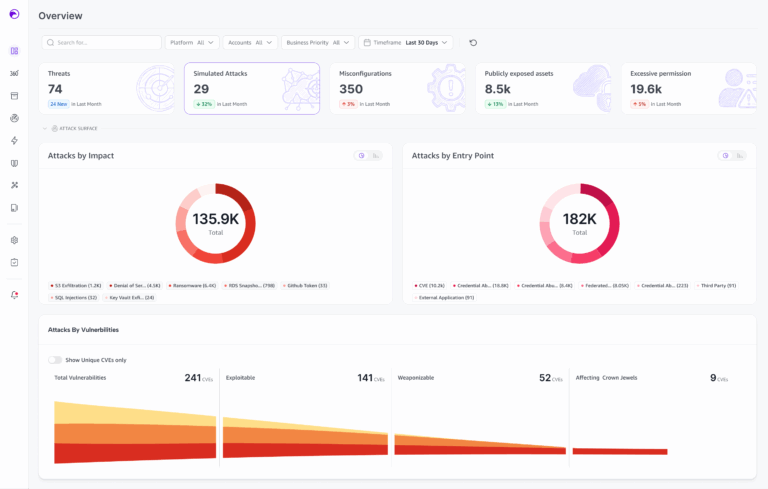
As we saw in the data, vulnerabilities are dramatically increasing in the cloud which has led to an increase in cloud breaches and attacks, which is a result of the challenge or prioritizing which vulnerabilities to handle. CNAPP Platforms identify these CVEs so they can be remediated. The issue is, the CNAPPs are identifying thousands, and thousands, and thousands of CVEs. Which ones need to be fixed? Which ones really put the business at risk? This is where Skyhawk can help.
Skyhawk’s Purple Team applies advanced adversary intelligent simulations to determine which CVEs put a crown jewel at risk, then the security team has two options:
The first is the easiest for the security team, they simply address the weaponized risk / vulnerability. Once it is remediated, the risk is eliminated.
However, there are times when remediation is not possible, at least not in a reasonable time, and this brings us to our second option. In that case the AI-based Blue Team can update detections and/or suggest automated response to stop the exploitation. This continuous preparation of your security controls prevents cloud breaches.
Skyhawk’s AI-based Purple Team runs continuously to continuously identify the weaponized vulnerabilities and CNAPP toxic combinations that can be weaponized by threat actors and then prioritizes them based on the business value of the asset to reduce business risk.
How does it work:
- Discover: Identifies all cloud assets and maps out the paths threat actors could use to gain access.
- Analyze: the configuration, vulnerabilities, and security controls that are in place are fully analyzed and attack recipes are created.
- Simulate Attacks: Leveraging the attack recipes, the Simulation Digital Twin is used to fully execute the attacks.
- Evaluate Defenses: Understand how defenses will respond and improve defenses to improve cloud security. This includes remediating vulnerabilities and posture alerts as well as updating permissions.
- Adapt: CDR machine learning models are updated for more accurate detections; pre-verified automated response is put in place for verified alerts.
Skyhawk Security has two ways you can try the product for free:
- You can try the product completely for free, for 30 days: sign up here!
- Our Purple Team Assessment will show you these weaponized threats prioritized by the business value of the asset in a comprehensive cloud security report based on the security of your cloud.