The common joke around security folks is that everyone knows what a password is, but remembering their own passwords is challenging. Despite these challenges, passwords are an essential security mechanism. NIST is updating its recommendations regarding passwords policy, presenting is an opportunity to learn why passwords were created and why do we need them.
How were the passwords invented and why do we need them at all?
How did the password come into our lives? In the early 1960s, MIT wanted to allow different researchers to work on the same mainframe computer (IBM 7094). For this purpose, they created different accounts for the users with different password for each user (I wonder- were these Pass0,Pass1, Pass2?). Since then, the password has remained one of the most basic information security measures. Today, with the internet and smartphones being an integral part of our everyday lives, we now use passwords all the time.
How does a password work? At the most basic level, the system we wish to access (let’s say – a Netflix account) has to create an account in our name. In order to log into the account, we will identify ourselves so that the system knows that it is us. To do this, we tell the system who we are (the username – usually it will be our email) and then we give it a piece of information that only we know – the password. The system will check that the password we entered matches the password associated with our user and if there’s a match, we will be allowed to log into the account.
Simple and easy. But sometimes, too easy.
Because people are always looking for shortcuts and have a limited ability to remember a lot of information, most of us will try to choose simple and easy passwords to memorize, something like “1234”, our name, or simply “password”. The problem is that over time hackers learned these habits and use this against us to easily hack into accounts. That’s why information security standards (primarily the previous NIST standard) decided to harden password policies and forced users to create passwords of minimal length (but not too long), to combine uppercase and lowercase letters, numbers and special characters. This criteria increases the complexity and reduces the chances of the password being guessed by hackers. Since attackers also started using robotic attacks that ran a large number of combinations in order to guess the password (called Brute force attacks) and also ran all the passwords they know from credential databases leaked (also called Dictionary attack), organizations also started demanding that users change their password frequently. All these restrictions were meant to reduce the chance that the password is hacked.
However, despite this criteria, studies have shown that users will still choose passwords that are as easy as possible. If they are required to change passwords often, they will simply recycle passwords from the past that are easy for them to remember. The bottom line is, many cyberattacks are still successful because hackers manage to penetrate accounts with guessed or obtained passwords.
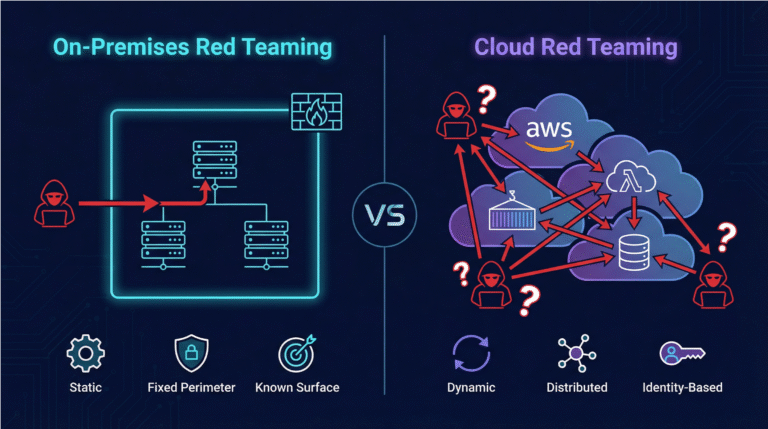
Passwords and the cloud
Who uses passwords in the cloud? All of us!
From Gmail to Netflix, from social accounts (Facebook and Instagram), to shopping apps, we all use passwords to access cloud systems. This makes them a prime target for hackers.
The new draft of NIST SP 800-63-4, which is a welcome update to the guidelines for managing digital identities, is expected to have a significant impact on cloud information systems and their security. A Google study found that more than 80% of cloud hacks used stolen credentials (including username and password). This is not surprising because close to half of Americans admitted that their passwords were stolen in the past year. In recent incidents, for example, software giant Snowflake was hacked. It was discovered that there was no periodic review of accounts to see if they were being used, so “older” accounts, even for some that no longer worked for the organization, had not been removed. Additionally, users were not forced to change passwords, which was problematic as for many accounts, this was the only form of protection. To combat these human behaviors, NIST now puts an emphasis on the following:
- Emphasis on multi-factor authentication (MFA): The draft encourages widespread use of multi-factor authentication and offers detailed guidelines for its implementation. Multi-factor authentication uses what you know (password) but also what you have (mobile device or authentication app) and reduces the chance of your account being compromised.
- Simplifying passwords: In contrast to previous approaches, the new draft reduces the emphasis on password complexity requirements (such as a combination of uppercase and lowercase letters, numbers and special characters). Instead, it emphasizes the importance of password length and the use of stronger authenticators. For example – instead of the password “Cloud1234” we can now create the password: “cloudy with a chance of meatballs”. The new policy allows spaces between words as part of the password. Another factor to reduce password reuse is offering a more flexible approach to the criteria of when a password need to be changes, for example, only requiring the a new password in case of a suspected security breach.
- Enhancing the security of API interfaces: Since cloud systems rely heavily on API interfaces, the demand for stronger authentication will lead to increasing the security of these interfaces. Specifically, at Skyhawk we’ve noticed that many organizations suffer from APIs keys leak and do not employ sufficient key rotation. Hopefully, the new recommendations will help improve that aspect of API security.
- Synchronous authentication: The draft offers detailed guidelines for synchronous authentication, which is a more secure method of identity verification. Synchronous authentication can be the use of a one-time code (OTP), which is a code that is randomly generated and sent to the user’s mobile phone. Other versions include the use of a physical hardware key that generates one-time codes and the use of biometric identification such as a fingerprint, facial recognition, or iris scanning.
- Improving identity and access management: The new guidelines will help organizations in the cloud improve their identity and access management, and ensure that only authorized people have access to information. We strongly recommend improving entitle management and conducting “what/if” simulation to determine proper entitlements.
How can Skyhawk help?
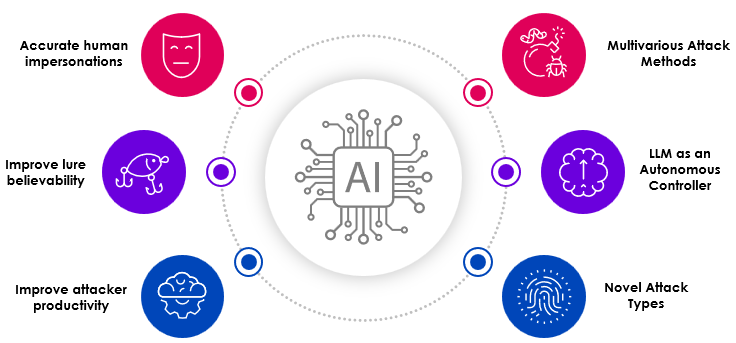
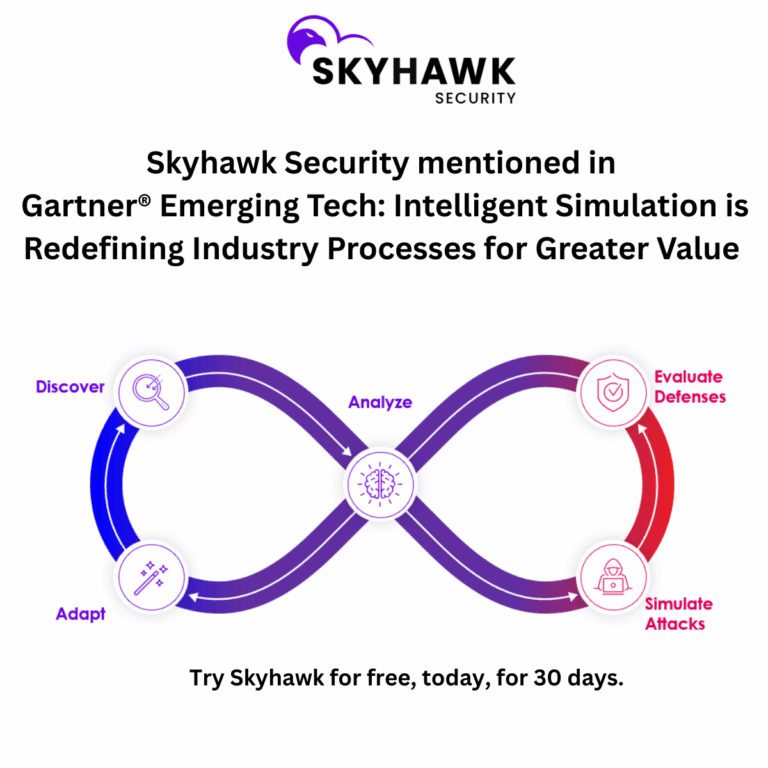
Skyhawk Synthesis Security Platform leverages three layers of advanced AI to detect threats to prevent breaches. As you saw in blog describing real customer incidents, most threat actors are not breaking in, they are logging in. If valid credentials are used, many security tools will miss the malicious activities that follow. Skyhawk looks at the behaviors, activities, and intent, to determine first, if something is out of the ordinary, and then, if it is malicious.
The AI-based Autonomous Purple Team can also help you identify potential attack paths and can surface abandoned permissions and credentials that could be used to advance an attack. It will proactively identify gaps in your cloud security, and then prioritize them based on the business value of the asset. It goes beyond toxic combinations by including the right context. Several vulnerabilities on an S3 bucket could look like an issue that should be prioritized, until you find out the S3 bucket is empty and is a road to nowhere. However, one single issue that leaves your customer database exposed is a significant weakness that needs to be addressed now – this is what the Purple Team will surface.
Want to try it out? Sign up for our free subscription today!