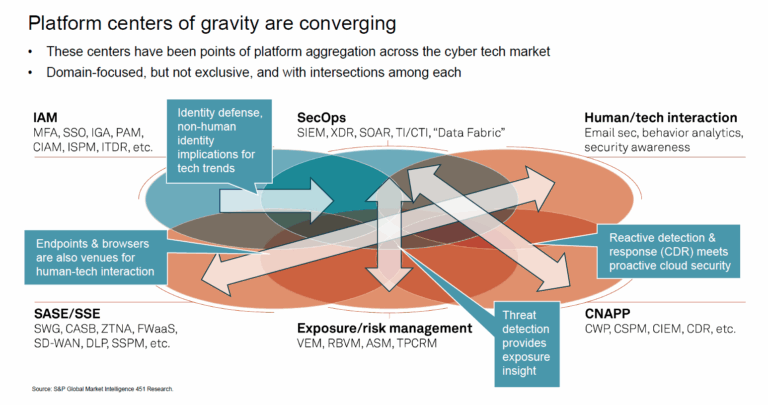
One of the reasons security teams are not successful is they are always looking back, looking back at the breach or the exposure or the alert. They are not able to look forward to prevent the breach, exposure, or alert from happening in the first place – until now. Skyhawk Security’s AI-based Autonomous Purple Team helps organizations predict the future and prevent the breach.
AI-based Simulation Twin
Skyhawk Security’s AI-based Purple Team leverages both AI-powered red and blue teams to simulate security breaches. This sophisticated simulation maps out all the paths to your most precious data assets—your crown jewels. The red team emulates threat actor behavior, while the blue team uses Skyhawk Security’s advanced cloud threat detection and response to counter these threats. All of this occurs within a Simulation Twin, an AI-based simulation environment, ensuring no real systems are affected and no erroneous alerts cause unnecessary panic.
What does this mean for Tabletop Exercises?
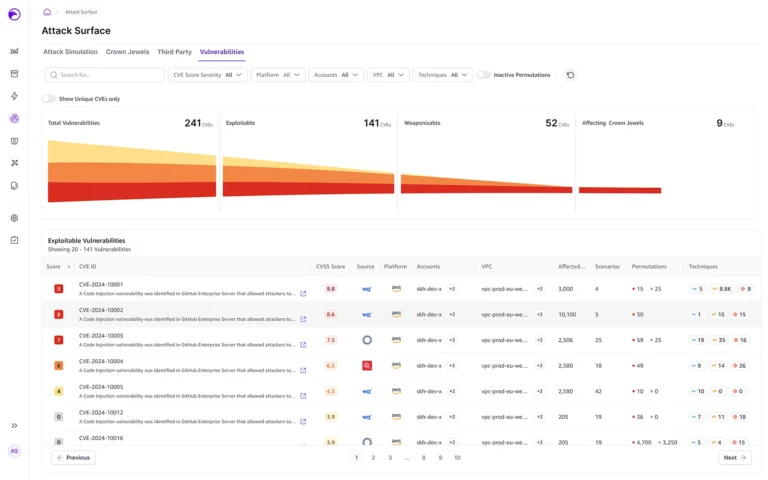
The Simulation Twin also revolutionizes Tabletop Exercises by providing comprehensive testing without the risk of overwhelming alerts. Like a digital twin, the simulation twin ensures production remains unaffected during the tests. Security teams experience the benefits of a thorough penetration or exposure test, identifying their vulnerabilities. Skyhawk goes a step further by prioritizing identified security issues based on the business value of the asset at risk. This means security teams not only pinpoint their risk exposures but also understand which critical assets are most vulnerable.
Confidently Leverage Auto-response and Auto-remediation
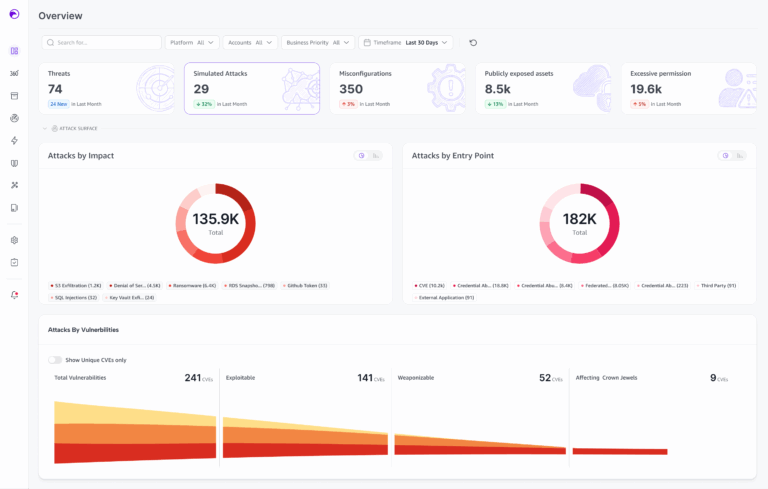
Security teams are overwhelmed by the sheer number of alerts and issues, with the average SOC receiving 4,487 alerts daily, according to Helpnet Security. An output of an AI-based Simulation Twin exercise includes recommended auto-response and auto-remediation strategies. These strategies can be rigorously rehearsed to ensure their effectiveness against potential threat vectors identified during the AI-based tabletop exercises. This repeated simulation ensures that the auto-response and auto-remediation configurations are thoroughly validated and reliable. The security team can trust the alert, and ensure it triggers the appropriate and validated auto-response through this testing.
Skyhawk Security’s Continuous Proactive Protection
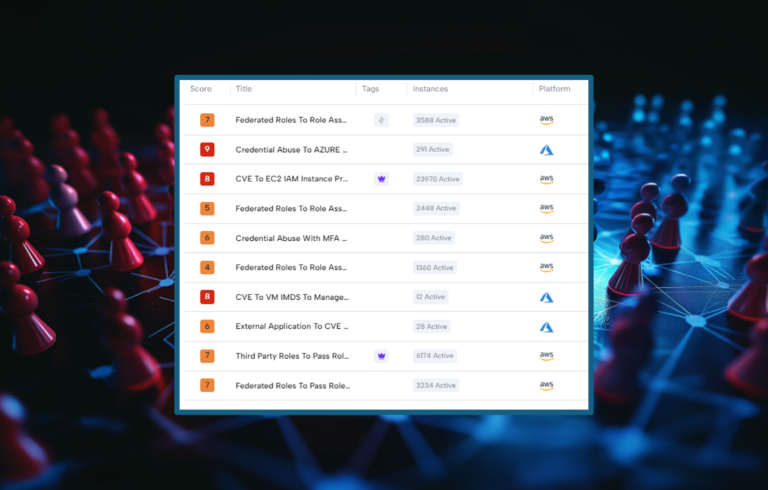
Skyhawk Security’s Continuous Proactive Protection, an AI-based Autonomous Purple Team, finds the most pressing issues in your cloud and then prioritizes them based on the business value of the asset behind the security issue.
- Discovers the environment’s inventory, configuration and identifies the crown jewels
- Analyzes the least resistant paths to the crown jewels
- Simulate attacks against the environment to identify gaps in security
- Understand how your defenses respond to the attack
- Adapt your threat detection to ensure it is aligned to your cloud infrastructure
This completely AI-based approach does not take a break and continuously evaluates your security to ensure your organization can fully take advantage of the cloud. As your cloud architecture changes to meet your changing business requirements, Skyhawk Security updates your security to align to your cloud architecture. It is continuously looking forward to identify where the easiest paths and entry points are in your cloud, and then prioritizes them, so you can take a proactive approach to your cloud security for the very first time.