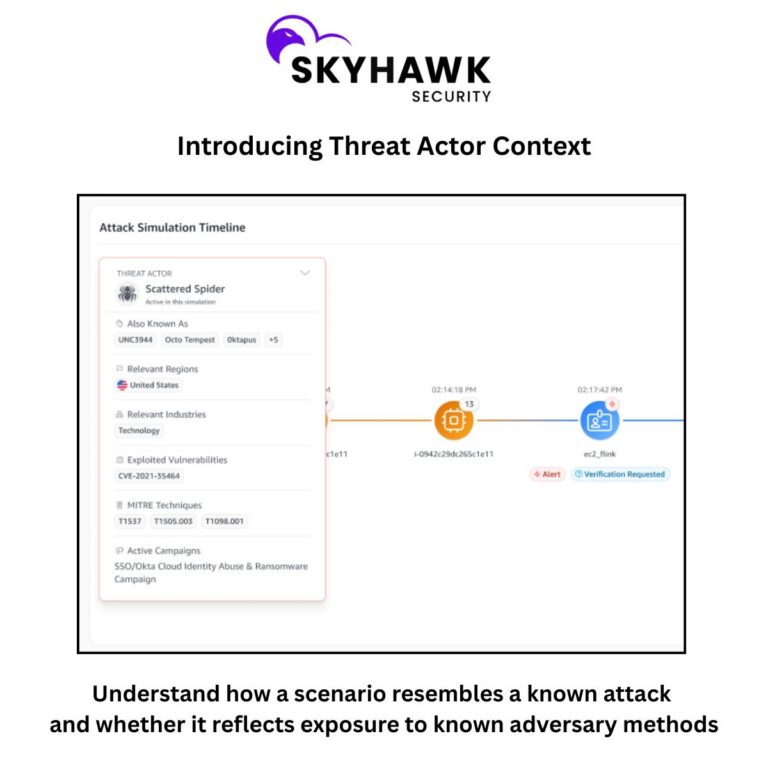
Cloud security teams are not short on alerts. They are short on insights. A finding may show risk of credential abuse, token theft, privilege escalation, or exfiltration to cloud storage. The technical signal is there. However, the question customers actually ask is much simpler: In what way does this matter to me? That is exactly what Threat Actor Context is built to answer.
Technical findings are not enough anymore.
Most cloud security platforms are good at surfacing alerts, but far fewer help customers understand what these alerts mean in the real world.
- A scenario may be technically valid but lack context
- Security teams are left translating raw steps into business relevance
- Executives need answers, are we exposed to the news headlines but hear technical language that does not connect to the threats they read about
- Customer-facing teams know findings are important but struggle to explain why it deserves attention now
What customers want is context so they can immediately understand:
- Does an exposure we have affiliated with a known threat actor pattern?
- Are we exposed to TTPs used in major campaigns?
- What is the blast radius of this risk/exposure I have
Enriching Adversary-view driven risk, with threat intelligence relevance information
Threat Actor Context enriches Skyhawk AI based attack scenarios with curated real-world context tied to known threat actors, major campaigns, and affiliated TTPs and Vulnerabilities exploited. In addition to showing the attack scenario from an adversary view, Skyhawk helps customers understand what that path resembles in the wild. Scenarios are now more than the TTPs used in the simulated attack; now they are enriched with context based on vertical, geography and more further helping in prioritization of risk based on business context.
For example, instead of showing: Credential abuse followed by access expansion and exfiltration to cloud storage. Skyhawk can help frame it as:
- This scenario resembles cloud identity abuse and exfiltration patterns associated with Scattered Spider activity seen in public intrusions such as MGM Resorts and Caesars Entertainment.
Or:
- This scenario reflects tradecraft associated with APT29, including patterns seen in NOBELIUM and TeamCity-related intrusion activity.
That changes the conversation immediately.
Why this matters?
Threat Actor Context helps customers move from technical analysis to meaningful insight. It helps them:
- Prioritize faster: Findings linked to recognizable adversary tradecraft stand out more clearly.
- Understand exposure: Customers can better assess whether their environment is exposed to methods associated with known actors and campaigns.
- Communicate with confidence: Threat context is easier to explain to leadership, customers, and stakeholders than raw technical behavior alone.
- See the bigger picture: The feature connects individual scenario steps to broader attacker patterns seen in the wild.
- Built on the signals that matter: Threat Actor Context draws on curated threat intelligence focused on cloud-relevant adversaries and campaigns. At a high level, this includes signals such as:
-
- Targeted geographies
-
- Targeted industries
-
- Known methods of operation
-
- Major public campaigns and intrusion patterns
-
- Affiliated TTPs and vulnerabilities exploited
-
- Cloud-focused tradecraft across identity, workloads, storage, SaaS, and access layers
This gives Skyhawk the ability to add real-world meaning to scenarios, not just more labels.
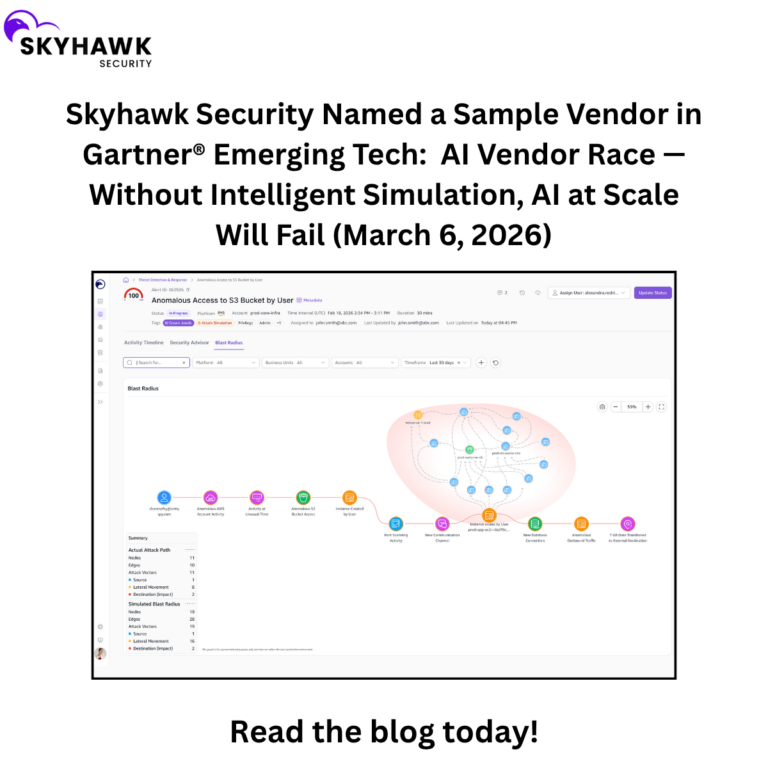
The question every customer asks after a big headline: Are we exposed to this?
Not whether a platform can run a forensic investigation. Not whether a vendor can make a courtroom-level attribution claim. They want to know whether the techniques associated with that actor or campaign could work in their cloud environment. Threat Actor Context helps answer that question in a practical, credible way.
Skyhawk’s new capability provides contextual relevance. It tells you quite clearly: This is what your environment is exposed to. This is what it resembles. This is why it matters. It delivers real-world context customers instantly recognize. This is where the feature becomes powerful.
As an example, Threat Actor Context can connect scenarios to recognizable adversary behavior such as:
- Scattered Spider patterns tied to identity-driven intrusions and high-profile attacks like MGM Resorts and Caesars Entertainment
- APT29 tradecraft linked to NOBELIUM and TeamCity-related cloud intrusion activity
- APT44 / Sandworm patterns associated with disruptive operations and campaigns like BadPilot
- TraderTraitor techniques tied to the JumpCloud compromise and the Bybit theft
- APT41 behavior associated with operations such as Operation CuckooBees and broader public sector targeting
Threat Actor Context delivers to customers something they urgently need: A clear understanding of what a scenario resembles and whether it reflects exposure to known adversary methods.
Skyhawk will demonstrate its capabilities at booth 358 in the South Expo Hall at the RSA Conference, taking place March 23 – 26, 2026, in San Francisco. Attendees can schedule a private meeting with the Skyhawk team using this link. For continuing updates follow Skyhawk Security on LinkedIn and Twitter.