This post was written by Rotem Klar, Product Manager at Skyhawk.
Above all else, security is a culture.
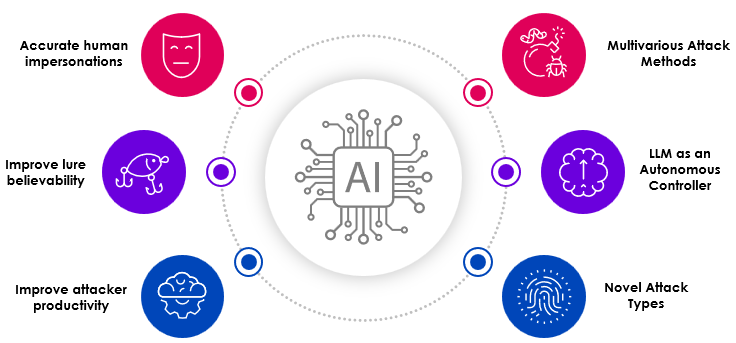
Companies who strive to develop the most sophisticated security solutions will need to participate in today’s security culture, keep up with the evolving cybercrime market, as well as talk the cyber-security language and be familiar with the common attack methodologies.
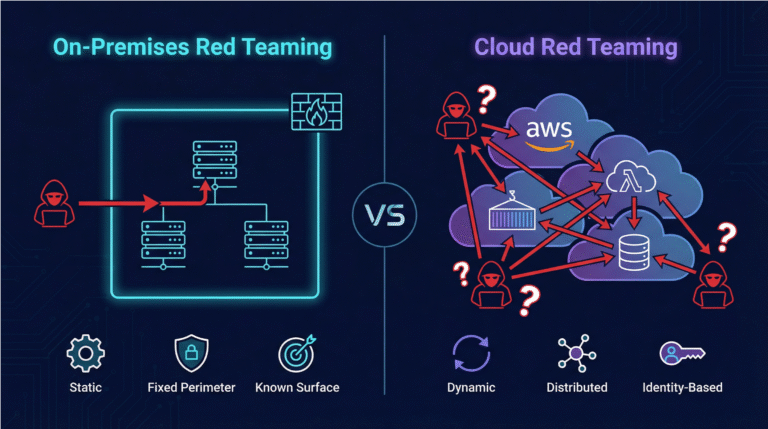
With the rapid adoption of cloud and companies being born in the cloud, this has become a challenge because a key characteristic (and benefit) of Cloud Computing is the speed of scalability.
Data is being moved and scaled at the highest speeds, visibility is then being highly challenged, keeping track of all your assets, configurations, and access management, which in turn result in endless vulnerability patching and investigating enormous amount of security alerts, these are all part of the bigger purpose and that is to achieve cyber security in the Cloud.
To cope, security teams approach this by using threat modeling. There are many well-established attack strategies and models in cybersecurity, but as seen in recent years, the framework that took over as the most popular of the intrusion frameworks, is
MITRE ATT&CKAtt&ck.
What is the MITRE ATT&CK Framework?
Mitre ATT&CK is a knowledge base and living framework of adversary tactics and techniques. It is globally-accessible and is based on real-world observations.
The MITRE Corporation developed MITRE ATT&CK framework in 2013 as a result of MITRE’s Fort Meade Experiment (FMX) where researchers emulated both adversary and defender behavior in an effort to improve post-compromise detection of threats through telemetry sensing and behavioral analysis. ATT&CK is working towards standardizing the terminology and naming of threat groups and attack methods from which the framework is derived from, and that creates a community and common language in the cybersecurity domain.
Over the past couple of years, ATT&CK became a popular reference for many organizations, from enterprises to the FBI (https://www.cisa.gov/uscert/ncas/alerts/aa20-296a) and government agencies around the world.
The ATT&CK framework supports businesses in risk management, research, and investigation as well as in aligning the terminology of threat detection, understanding attacker behaviors, how to classify, prioritize and mitigate threats, and ultimately can help to effectively secure a business against compromise.
MITRE ATT&CK (Adversarial Tactics, Techniques, and Common Knowledge) organizes adversaries’ behaviors into a series of tactics (specific technical objectives that an attacker wants to achieve) and within each tactic category, ATT&CK defines a series of techniques (which describe how an adversary may try to achieve that objective). Examples of tactics are Defense Evasion, Lateral Movement, and Exfiltration. ATT&CK also includes procedures which detail known implementations of a particular Technique or Sub-Technique. Tactics, techniques and procedures are commonly referred to as TTPs.
ATT&CK knowledge base is based on extensive research and open-source public reporting, which means the more people are reporting, and the more ATT&CK investigates, the “encyclopedia” database is continuously being updated.
What is the MITRE ATT&CK Cloud Matrix?
The ATT&CK framework-model is based on matrices. Attackers move across the matrices, choosing tactics and techniques that enable them to accomplish their desired goal.
The main matrices of ATT&CK cover 3 main Technology Domains: Enterprise, Mobile, and ICS.
As part of the Enterprise matrix, ATT&CK dedicated a sub-matrix for the Cloud technology domain. The Cloud matrix covers cloud-based techniques and contains information for the following platforms: Azure AD, Office 365, Google Workspace, SaaS, IaaS. As Cloud usage becomes more prevalent, it comes as an advantage to use a framework that is specifically tailored for cloud computing and its inherent threats.
4 Most Common Use Cases of MITRE ATT&CK
There are several use cases for the MITRE ATT&CK framework, the most common being:
- Detection and Analytics – ATT&CK can help cyber defenders develop analytics that detect the techniques used by an adversary. ATT&CK provides guidance to what data should be collected, from which source, how to search it, and how to analyze it for detection and analytics.
- Threat Intelligence – ATT&CK gives analysts a common language to structure, compare, and analyze threat intelligence. Intelligence is based on what an adversary will do and utilizing that information to improve how you will react to it on time. ATT&CK provides structure to the often-chaotic naming of adversary groups and behaviors so users can investigate more easily suspicious events. Those in turn might have already been observed by the community, mapped to ATT&CK and even been attributed to an adversary group.
- Assessment – ATT&CK enables assessment organization’s defenses by determining the coverage for each technique in ATT&CK, identifying the highest priority gaps, and modifying accordingly the defenses to address those gaps.
- Adversary Emulation and Red Teaming – Naturally, ATT&CK will be useful for adversary emulation and red teaming by choosing an ATT&CK technique, for which a test procedure will be executed, analyzing detections of that procedure, and making improvements to the defenses.
How Skyhawk Security is using MITRE ATT&CK to enhance its Threat Detection and Response
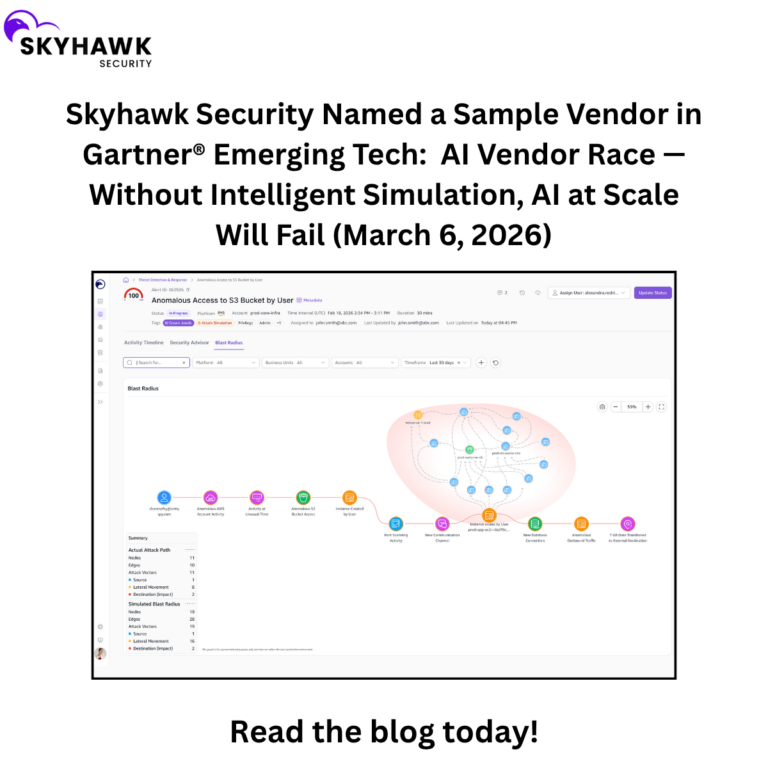
Skyhawk Security, being a cloud-native security platform, uses MITRE ATT&CK’s Cloud data to advance its CTDR capabilities.
Skyhawk uses MITRE ATT&CK to look at the problem from the perspective of the adversary. To understand how adversaries might operate so you can plan how to detect or stop that behavior.
3 main ways Skyhawk is using ATT&CK’s Cloud knowledge base:
- Skyhawk Synthesis identifies anomalies and malicious events against resources that are categorized by ATT&CK as TTPs. The information supplied by ATT&CK supports Skyhawk Synthesis in contextualizing the events, risk assessment, and prioritization. Skyhawk Synthesis correlates the detected events to create attack paths that can be mapped on the ATT&CK Cloud Matrix and can then be used for further investigation and mitigation.
- Skyhawk Security’s platform visualizes the attack paths to improve detection of attacks in progress, support investigation, and carry out countermeasures.
- Skyhawk Synthesis is continuously aligned to the common language and terminology created by MITRE ATT&CK, by which the platform’s alerts, events, and attack paths are categorized and tagged.
Skyhawk Security’s MITRE ATT&CK EDGE
According to published research, it has been recorded that Large- and medium-sized enterprises are faced with challenges when trying to implement the ATT&CK framework in their security products to identify, protect, detect and respond to threats.
Skyhawk Security has successfully achieved alignment to the MITRE ATT&CK framework, implemented the common use cases in its platform, and is enhancing its CTDR continuously.