How Skyhawk Security and Tenable Joined Forces to Silence the 99% and Surface What Actually Matters

Security teams are drowning. Vulnerability management platforms do exactly what they are designed to do, they surface every exposure, score it, and hand it to the security team to remediate. The problem is that in a modern cloud environment, that list can contain hundreds of thousands of vulnerabilities. And the uncomfortable truth is that fewer than 1% of them represent […]
Skyhawk Security Ties AI Red Team Cloud Attack Scenarios to Known Threat Actor Tradecraft

New capability helps security teams prioritize exposures and simulated AI red team attack scenarios based on threat Intelligence RSA CONFERENCE, San Francisco, March 24, 2026 – Skyhawk Security, the leader in Purple Team-powered cloud security, has added Threat Actor Context to its award-winning platform. The enhancement adds real-world adversary insights to cloud attack scenarios created […]
Meet Threat Actor Context: Turn Cloud Findings Into Real-World Threat Exposure
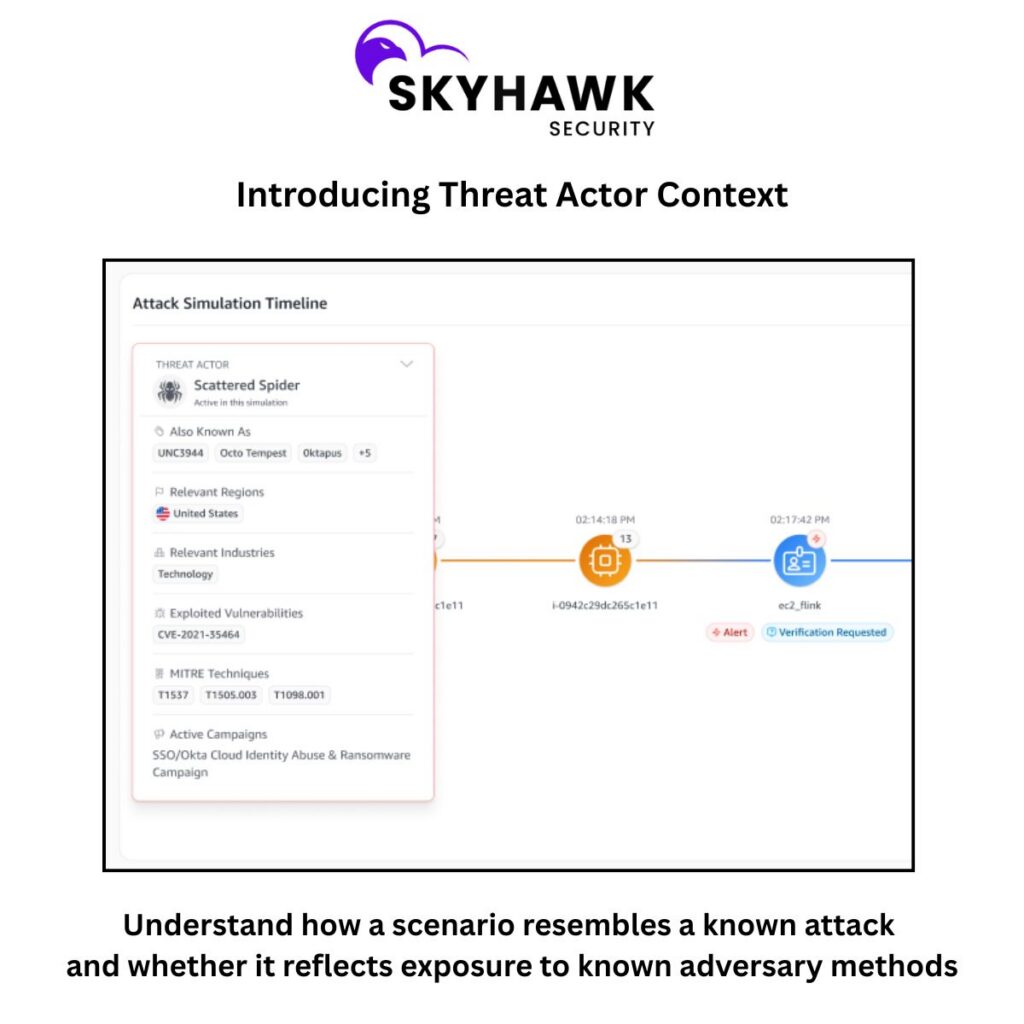
Cloud security teams are not short on alerts. They are short on insights. A finding may show risk of credential abuse, token theft, privilege escalation, or exfiltration to cloud storage. The technical signal is there. However, the question customers actually ask is much simpler: In what way does this matter to me? That is exactly what Threat Actor Context is built to answer. Technical findings are not enough anymore. Most cloud security platforms are […]
Skyhawk Security Named a Sample Vendor in Gartner® Emerging Tech: AI Vendor Race — Without Intelligent Simulation, AI at Scale Will Fail (March 6, 2026)
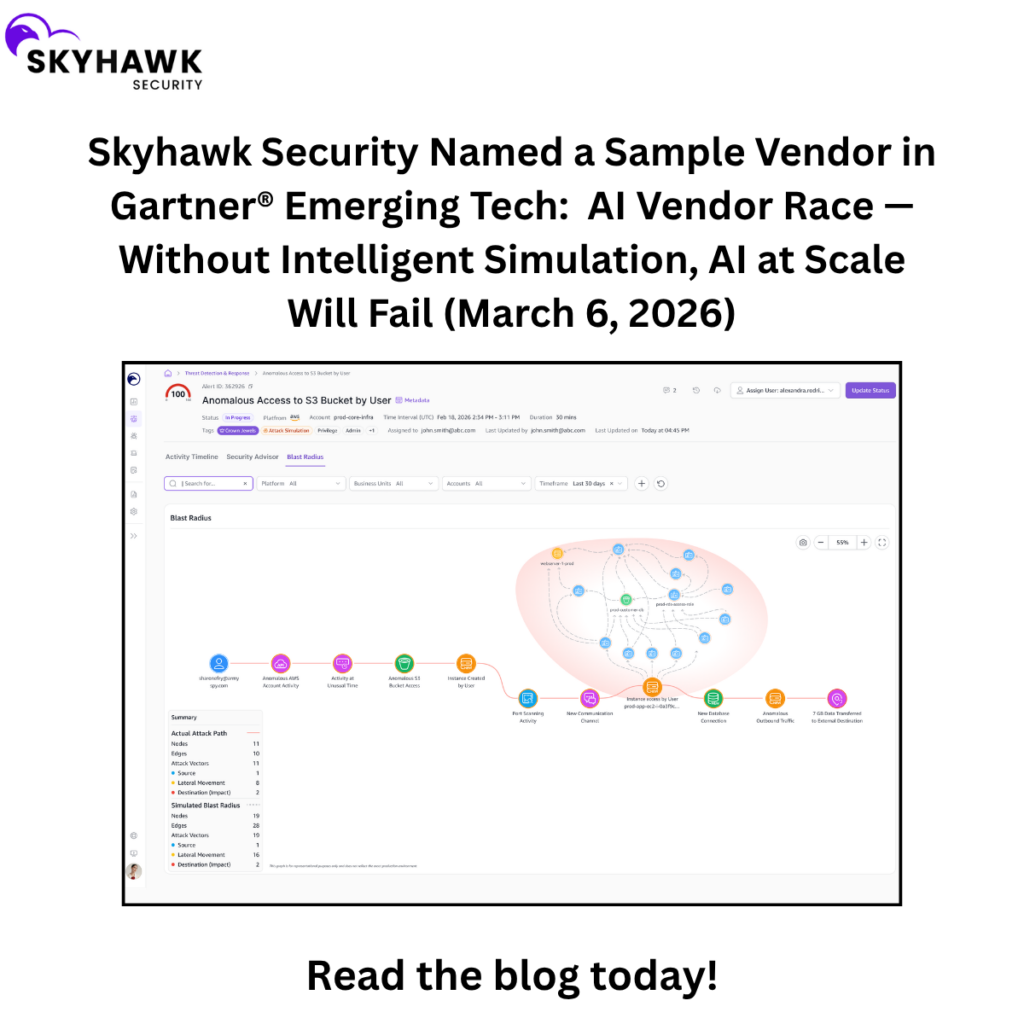
Organizations, especially security teams, are not just going to go with a recommendation from an AI platform. An Intelligent Simulation that shows what will happen, why, and how gives security teams the confidence that what they are looking at is feasible and needs to be addressed. This is why it is so critical to the […]
Skyhawk Security Overview

Skyhawk Security is the leader in AI Based Purple Team-Powered Cloud Security, leveraging a multi-layer AI-based approach to identify and preemptively stop cloud threats before they become breaches. Skyhawk revolutionizes cloud security with its Continuous Proactive Protection, an AI-powered Autonomous Purple Team, enabling security teams to take a proactive approach to cloud security for the […]
Eliminate Alert Overload: Achieve True Cloud Risk Reduction

Table of Contents This blog is a summary of our panel webinar, Eliminate Alert Overload: How to Achieve True Cloud Risk Reduction. The Cloud Security Crisis No One Is Talking About Loudly Enough Ask any CISO what keeps them up at night and the answer is rarely “we don’t have enough security tools.” More […]
Skyhawk Security Wins Security Innovator of the Year in SiliconANGLE Media’s Tech Innovation CUBEd Awards

TEL AVIV, Israel, February 24, 2026 – Skyhawk Security, the leader in Purple Team-Powered Cloud Security, has been named Security Innovator of the Year by SiliconANGLE Media’s 2026 Tech Innovation CUBEd Awards. theCUBEd Awards is an annual program honoring the most innovative companies, technologies and leaders shaping the future of B2B and B2B2C technology. This […]
Skyhawk Security Appoints Jason Schaaf as Chief Revenue Officer

Cybersecurity sales veteran who scaled CyberX through Microsoft acquisition, drove growth at ActiveFence, joins Skyhawk to lead global go-to-market strategy TEL AVIV, Israel, February 18, 2026 — Skyhawk Security, the leader in Purple Team-Powered Cloud Security, today announced the appointment of Jason Schaaf as Chief Revenue Officer. Schaaf will lead Skyhawk’s global go-to-market organization—including sales, […]
Mind the Gap: Why your on-prem Red Team isn’t Cloud-Ready
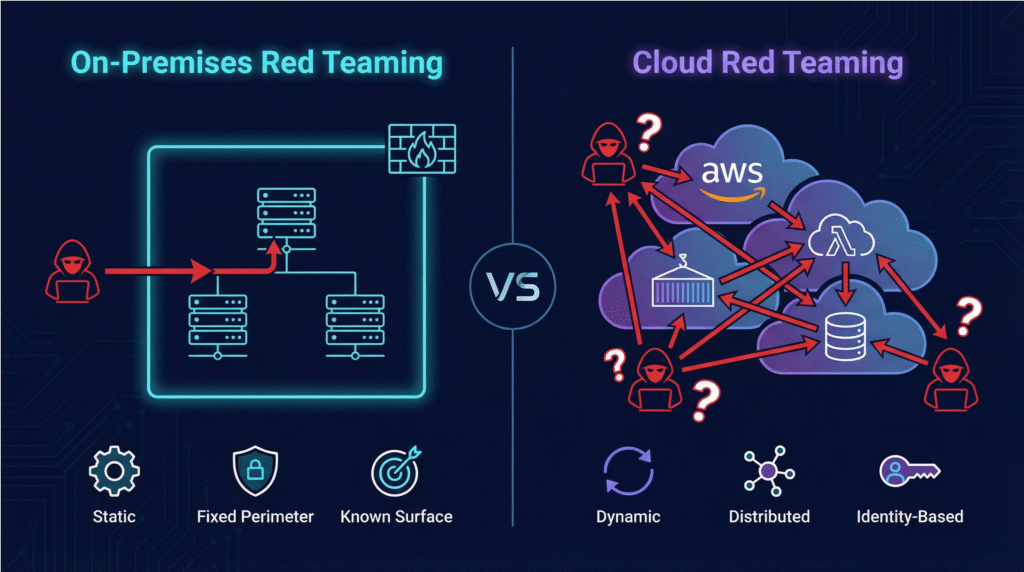
Red teaming is a key pillar of a modern cybersecurity strategy. By emulating the tactics, techniques, and procedures (TTPs) of real-world attackers, organizations can test their defenses and readiness for a potential breach. Industry data shows that a significant 74% of organizations perform red team exercises regularly. However, a critical and often underestimated challenge has […]
Fight AI-based Threats with AI-based Security
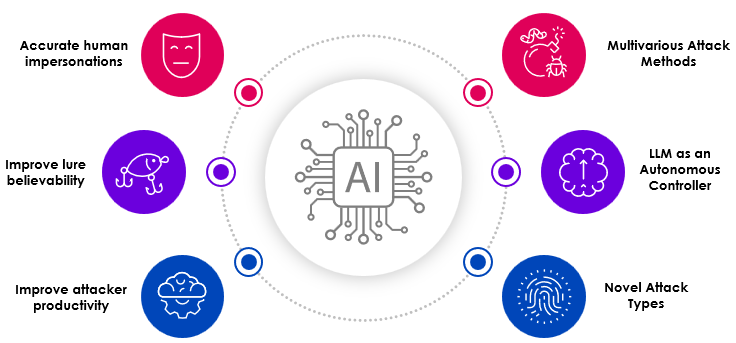
Threat actors are using AI to create better, faster and stronger attacks. AI can create a threat actor army with just a few prompts (Check out this attack detected by Anthropic) that looks for vulnerabilities across your cloud attack surface to breach your cloud. If you are not using AI to defend your cloud, you […]