The cybersecurity community has been watching Project Glasswing closely — the largest multi-party vulnerability coordination effort in history. Now, with the emergence of Mythos, the stakes have escalated dramatically. Mythos is not just another vulnerability scanner. It is an AI-powered system capable of discovering vulnerabilities and generating working exploits at a speed and scale that no security team has ever had to contend with before.
The result? A coming wave of disclosures, many accompanied by functional exploits generated in near real time, that will hit every organization simultaneously. The remediation backlog this creates will be unlike anything the industry has seen. And the teams that try to address it by simply working harder, faster, or with more automation will find themselves losing ground.
The answer is not more remediation effort. The answer is precision.
The Problem with “Do I Have This Vulnerability?”
When a new CVE drops, the instinctive question from every security team is: “Do we have this?” In a post-Mythos world, the answer will almost always be yes. Mythos is designed to find vulnerabilities broadly and quickly, and the volume of findings it surfaces will be staggering.
But “do I have this vulnerability?” is the wrong question. It is a question that leads directly to an unmanageable remediation backlog, one where teams spend enormous effort patching findings that, in their specific environment, represent no real threat to the business.
The right question is: Given my specific environment, does this vulnerability represent a real, end-to-end attack path to something that actually matters?
That is a fundamentally different question. And it requires a fundamentally different kind of analysis.
Weaponization Risk Is Context-Dependent
The same vulnerability does not create the same risk for every organization. A finding that represents a direct, exploitable path to crown jewels in one environment may be a dead end in another. Determining which scenario applies to your organization requires a multi-layer analysis that generic scanners simply cannot perform:
- The application itself: How it is built, what data it handles, and what it is connected to
- The infrastructure it runs on: Cloud configuration, compute, storage, and network architecture
- IAM and permission structures: Which identities have access to what, and which of those permissions have never been used but could be weaponized
- Micro-segmentation: Whether lateral movement between the vulnerability and a high-value asset is actually possible
- Compensating controls: What detective and preventive controls are already in place that would interrupt an attack chain before it reaches impact
Without this context, a vulnerability finding is just a data point. It tells you something exists. It does not tell you whether it matters.
The 1% Principle
Skyhawk Security’s experience running continuous adversarial simulation across customer environments consistently reveals a striking pattern: fewer than 1% of discovered vulnerabilities represent a viable, end-to-end attack path to a high-value asset. The other 99% are real vulnerabilities but they are not actionable threats in the specific context of that organization’s environment.
This is not a reason for complacency. It is a reason for precision. When Mythos surfaces thousands of new findings, the organizations that will respond effectively are the ones that already know which findings fall into that 1% and which 99% can be addressed on a normal remediation schedule without triggering a crisis response.
Check out webinar to hear from Amir Levran, CISO, SundaySky on how Skyhawk Security focuses his team on just 0.3% of his alerts.
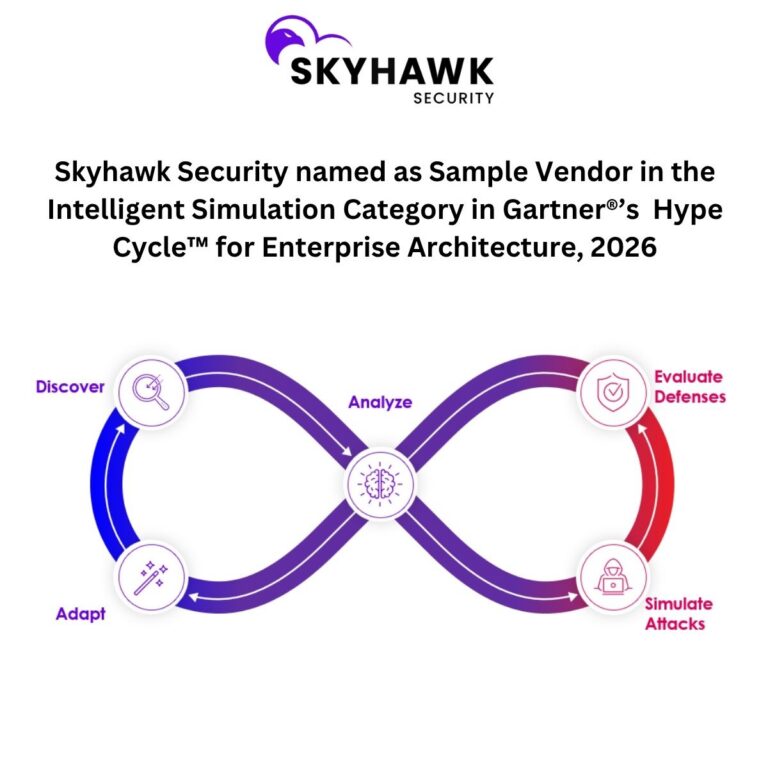
How Skyhawk’s AI Red Team Cuts Through the Noise
Skyhawk Security’s AI Red Team is purpose-built for exactly this challenge. Rather than generating a list of vulnerabilities and leaving the prioritization to the human team, the AI Red Team operates as a continuous, autonomous adversary that simulates real attack scenarios against a digital twin of the customer’s live environment.
For every new vulnerability that surfaces, including those surfaced by Mythos, the AI Red Team does not simply ask “does this exist?” It asks: “Can this vulnerability be weaponized in this specific environment, against this specific asset, given the current IAM configuration, compensating controls, and network architecture?”
It then traces the full attack path from initial exposure to potential business impact.
This process is non-disruptive by design. All simulation runs against the digital twin, never against production systems. It is continuous, meaning it does not wait for a scheduled assessment or a new CVE to trigger a review. And it is contextual with every finding evaluated against the customer’s specific environment, not a generic threat model.
The output is not a list of vulnerabilities. It is a prioritized, context-aware view of the findings that represent real risk to that organization. Typically, fewer than 1% of the total alerts, along with a clear understanding of the blast radius, the attack chain, and the compensating controls available while remediation is underway.
A Word of Caution on Automated Remediation
As the volume of Mythos-driven findings grows, the temptation to respond with automated remediation will be significant. Automation has a role to play but only when it understands the context it is operating in.
Automated remediation applied without understanding blast radius, asset value, and compensating controls can create new risk while closing an old one. A configuration change that patches one vulnerability may inadvertently break a compensating control that was protecting against three others. An automated fix applied to a production workload without understanding its dependencies can cause outages that cost more than the vulnerability it was meant to address.
The same principle that applies to prioritization applies to remediation: context is everything. Automation that lacks context does not reduce risk. It redistributes it.
The Questions That Actually Matter
When the next Mythos disclosure lands, Skyhawk helps security teams answer the questions that actually drive risk reduction:
For the new vulnerability just discovered:
- How is my specific environment exposed to it?
- Is there a real asset at risk, and what is the business impact if it is exploited?
- Does a viable end-to-end attack path exist from this vulnerability to that asset?
- What compensating controls do I have in place while remediation is underway?
These are the questions that separate organizations that manage risk from organizations that manage lists.
Precision Over Volume
The Mythos alert tsunami is coming. The organizations that get ahead of it will not be the ones with the largest remediation teams or the most aggressive patching schedules. They will be the ones who know, with confidence, which 1% of findings represent real risk to their business, and who can act on that 1% with speed and precision while the other 99% are addressed on a rational, prioritized schedule.
That is what Skyhawk Security’s AI Red Team delivers. Not more alerts. Not a longer list. A precise, context-aware answer to the question that actually matters: what do I need to act on today?
Check out our webinar on Mythos and the Glasswing Project.