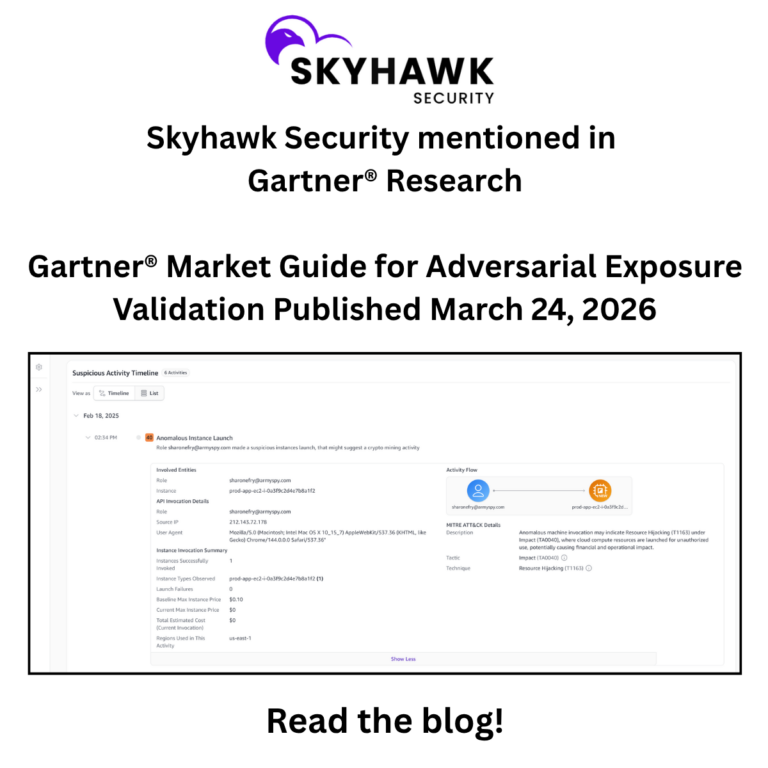
Skyhawk Security’s AI Red Team identifies the exposures that adversaries will exploit to breach your cloud. Skyhawk Security takes this analysis one step further by prioritizing those exposures based on the business value of the at-risk asset. According to the research: “Gartner defines Adversarial Exposure Validation (AEV) as technologies that deliver consistent, continuous and automated evidence of the feasibility of an attack”, which in our opinion, aligns very well with Skyhawk’s AI Red Team.
In this Market Guide, Gartner has gone further by stating that, “AEV as a market category replaces breach and attack simulation (BAS) and automated penetration testing and red teaming technology from the 2023 Gartner Hype Cycle (Hype Cycle for Security Operations, 2023).” Skyhawk Security helps operationalize CTEM to help organizations continuously reduce their exposure for true cloud risk reduction.
Adversarial Exposure Validation
As mentioned, Gartner defines AEV as technologies that deliver “consistent, continuous and automated evidence of the feasibility of an attack”, which we consider proves exploitation rather than theorizing about it. And in our opinion, Skyhawk Security does exactly this. The AI-based Red Team creates attacks based on the cloud architecture and security controls and proves what threat actors can breach in your cloud. As per Gartner, “EAP solutions continuously discover, assess and prioritize exposures with context such as business, asset criticality and threats that pose the greatest risk, commonly covering all assets in an environment. In contrast, AEV solutions tend to focus on proving exploitation of high-value vulnerabilities or threat scenarios that lead to successful attacks related to their validation functions.” In our opinion, this directly validates Skyhawk’s differentiated positioning against CNAPPs and vulnerability management tools.
Gartner notes, “EAP solutions provide broader and more up-to-date information about exposures, and some can predict the likelihood and potential impact of exploitation through passive modeling. However, they can’t offer direct evidence on whether the vulnerability or other exposure is actually exploitable within an organization’s security posture/controls. They also can’t provide context on the blast radius of the exposure.”
We believe, Skyhawk Security not only provides evidence that the exposure is exploitable with the technical detail of how an attack scenario works, but it also highlights how internal or external SOC members responded to the simulated attack. The AI-based Purple Team enables SOC pre-training so that organizations can respond quickly and effectively.
Skyhawk Security’s Approach Eliminates Alert Fatigue
Organizations that have traditional vulnerability management programs have an overwhelming number of findings. We heard from a prospect at re: Invent who had 16 million findings within their CNAPP – 16 million!! AEV techniques reduce that volume by confirming and prioritizing findings through offensive-testing techniques. This is the exact problem Skyhawk solves, reducing 500,000 CVEs to 7 actionable threats. Check out this blog to hear from a customer who was able to reduce their CNAPP findings by 99.7%.
“For many organizations that are dealing with the outputs of a traditional vulnerability management (VM) program, the volume of findings is high. Validation techniques allow security operations teams to reduce that volume by confirming and prioritizing findings through offensive-testing techniques.”
Digital Twin Deployment Ensures Non-Disruptive Validation
Gartner’s states, “AEV platforms supports multiple execution environments that determine where validation occurs” and goes further to define Digital Twin as: “A replica of the production environment that mirrors relevant assets, identities, configurations, traffic and security controls. Digital twins enable safe execution against high‑risk or mission‑critical assets without impacting live operations.”
In our opinion, this validates Skyhawk’s non-disruptive, digital twin simulation approach. Please check out our platform page for more information on our non-disruptive simulation.
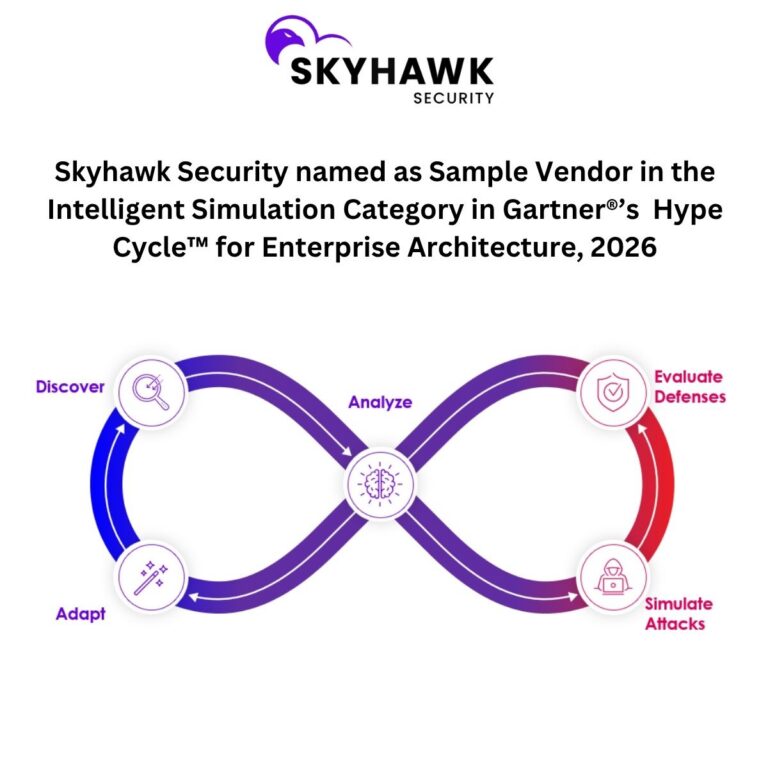
AI-Powered Attack Scenario Generation Is the Future of the Market
Gartner notes, “AEV platforms increasingly leverage AI to improve scalability, adaptability, and operational relevance by incorporating LLMs and AI agents within the control plane to assist with scenario selection, prioritization and interpretation of results to support decision making.”
In our opinion, this validates Skyhawk’s Adversarial AI engine which creates custom attack scenarios for each customer based on their security controls and cloud security architecture. It leverages threat intelligence, exposure data and then prioritizes the attack scenario results based on the business value of the exposed asset. Additionally, a recent CrowdStrike Report shows that AI-based attacks are up 89% year over year, and organizations need to respond at machine speed to stop these attacks. This is why it is critical for security teams to incorporate an AI-based Security Platform in their security strategy.
Continuous Testing Is Now a Gartner Recommendation
Gartner’s Strategic Planning Assumptions states: “By 2029, 60% of organizations will have adopted a structured exposure validation practice as part of CTEM, with AEV technologies and managed service providers serving as primary enablers.”
Skyhawk’s opinion is our Continuous Proactive Protection Platform is purpose-built for exactly this use case, continuous, automated, AI-driven validation. Please see our whitepaper on how Skyhawk Security operationalizes CTEM.
Summary
AI Autonomous Attacks are on the rise, and the cloud is the target. Skyhawk Security’s AI-based Purple Team provides a comprehensive approach to cloud security, delivering “left of boom” preemptive security. The AI Red Team proves which exposures can be weaponized to breach your cloud, and then prioritizes those exposures based on the business value of the at-risk asset. Additionally, Skyhawk delivers “right of boom” with the ability to validate security controls and pre-train the SOC team on real attack scenarios so response is instinct, not improvisation.
Gartner subscribers can read the full report at www.gartner.com.
Gartner Market Guide for Adversarial Exposure Validation by Dhivya Polle, Mitchell Schneider, Eric Ahlm published March 24, 2026.
Gartner does not endorse any company, vendor, product or service depicted in its publications, and does not advise technology users to select only those vendors with the highest ratings or other designation. Gartner publications consist of the opinions of Gartner’s business and technology insights organization and should not be construed as statements of fact. Gartner disclaims all warranties, expressed or implied, with respect to this publication, including any warranties of merchantability or fitness for a particular purpose.
GARTNER is a trademark of Gartner, Inc. and its affiliates.