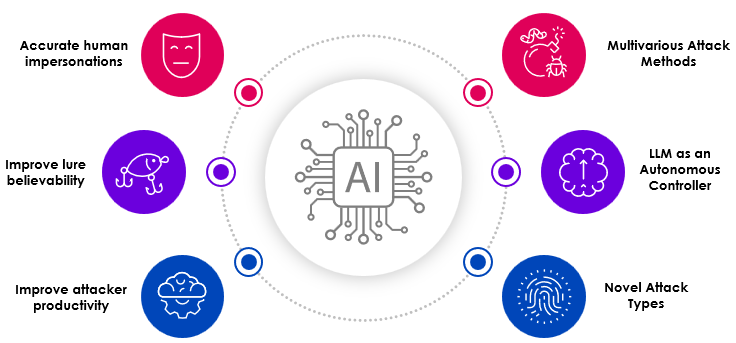
If you watched 60 minutes last week, or caught Anthropic’s report on “Disrupting the first reported AI-orchestrated cyber espionage campaign”. This is something we have been discussing at Skyhawk for a while. Please review this blog for to understand the impact of AI.
What happened?
In September of this year, Anthropic detected a cyber espionage operation conducted by a state-sponsored group, which they named GTG-1002, and they believe this is the first documented case of a cyberattack largely executed without human intervention at scale.
The report discusses how Claude did the majority of the work autonomously with the human only investing 10 minutes of time1. At Skyhawk, we knew we would see when we discussed Fighting AI with AI. If you look at the tasks in the table, it would a human days to do this work if they had to do this on their own. For example, mapping the entire attack surface involves a systematic, multi-step process to identify, catalog, and analyze all potential entry points where an attacker could gain unauthorized access to an organization’s digital and physical environments. With AI, this is only 20% of the overall work in the table above, and it was completed in minutes. Threat actors are able to dramatically improve their productivity using AI to execute the tedious work of an attack. Skyhawk’s Platform prepares your cloud security defenses for these aggressive and accurate AI-based attacks.
As stated in the report: “Exploitation proceeded through automated testing of identified attack surfaces with validation via callback communication systems. Claude was directed to independently generate attack payloads tailored to discovered vulnerabilities, execute testing through remote command interfaces, and analyze responses to determine exploitability2.”
Example: Vulnerability discovery and exploitation sequence3
| Claude’s autonomous actions
(1-4 hours) |
Human operator actions
(2-10 minutes) |
|---|---|
Task 1: Discovery
|
Reviews AI findings and recommendations Approves exploitation |
Task 2: Vulnerability Analysis
|
|
Task 3: Exploit Development
|
|
Task 4: Exploit Delivery
|
|
Task 5: Post-Exploitation
|
While the report mentions Claude often overstated findings and hallucinated throughout the attack, it still improved productivity of the attacker and it will continue to improve over time4. This will make it difficult for attackers to have fully autonomous attacks, however, this is the case today. We do not know when we will see a successful, fully autonomous attack, but it looks like not too far in the future.
How Skyhawk can help?
Skyhawk can help security teams in several ways.
First, reduce the number of blind spots. We hear from our customers that this was an issue. We have also heard that we have uniquely solved this issue. Skyhawk doesn’t show you just “what is under the flashlight.” Our use of AI locates all cloud assets – so you will not miss a threat, vulnerability, or exposure in your cloud.
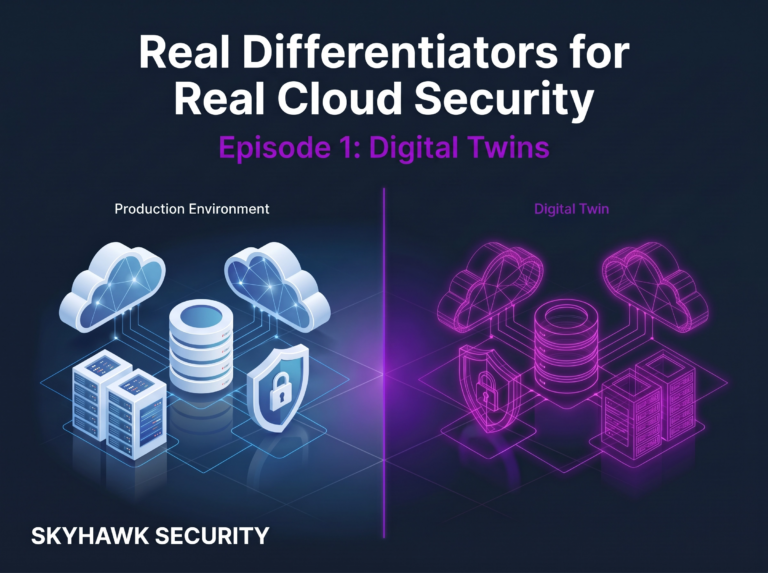
Second, Skyhawk prepares your defenses and your team for the attacks that will be successful in your cloud. Our AI-based Purple Team designs attacks rehearsals, specific for your cloud architecture and your cloud security controls. We do not use pre-scripted attacks – as this will not prepare the platform and it will contribute to the first problem, only showing you what is under the flashlight.
Third, measure drift in detection rates from existing controls. Skyhawk does this in two ways.
- AI-based Blue Team (CDR): Our CDR leverages several layers of machine learning models which are updated daily. This ensures alignment with your cloud architecture and most likely threats.
- AI-based Red Team: Delivers an adversarial view of vulnerabilities, identifying the “low hanging fruit” threat actors will go after first.
Finally, the most important aspect of the Purple Team is it is autonomous. It is continuously learning based on your cloud architecture, security controls, and the threats to your cloud – and doing this specifically for your cloud. As mentioned, nothing is pre-scripted – it is cloud security designed for your cloud.
Are you going to re:Invent? We are too! Book a meeting with us.
You can also try Skyhawk Security for free for 30 days. Let us find the AI-based threats for you, today.
1,2,3,4Disrupting the first reported AI-orchestrated cyber espionage campaign