SEC Cyber Rule: A Primer for Practitioners by Alex Sharpe

Please check out this guest blog post by Alex Sharpe, a Cyber Security Expert with decades of experience. The SEC Cybersecurity Rule is designed to provide transparency so investors can make information decisions. The rule effectively imposes two requirements on publicly traded companies. The full rule can be found here. The SEC has three missions: […]
Fight AI-based Threats with AI-based Security
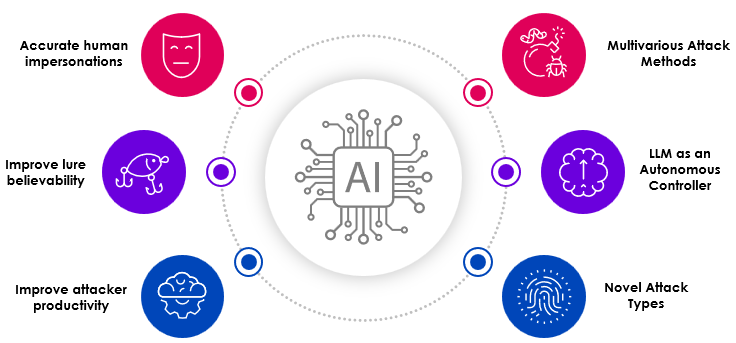
Security teams are quickly realizing the benefits of Generative AI and are incorporating this technology into their security products for earlier detection of risks in the environment. AI can help security teams better recognize and resolve threats and exposures in their cloud environment. However, threat actors have also realized that AI offers them benefits as […]
AWS re: Invent 2023 recap

Can you believe that re: Invent ended only 10 days ago! Skyhawk had a great event – great conversations, a great product launch and lots of coverage. So, what did we learn? Purple team is “the perfect use case for Generative AI”. We heard this from industry experts, customers, and prospects. Continuous Proactive Protection is […]
Verified Alerts are the Alerts that Matter: Operationally Efficient Cloud Breach Prevention
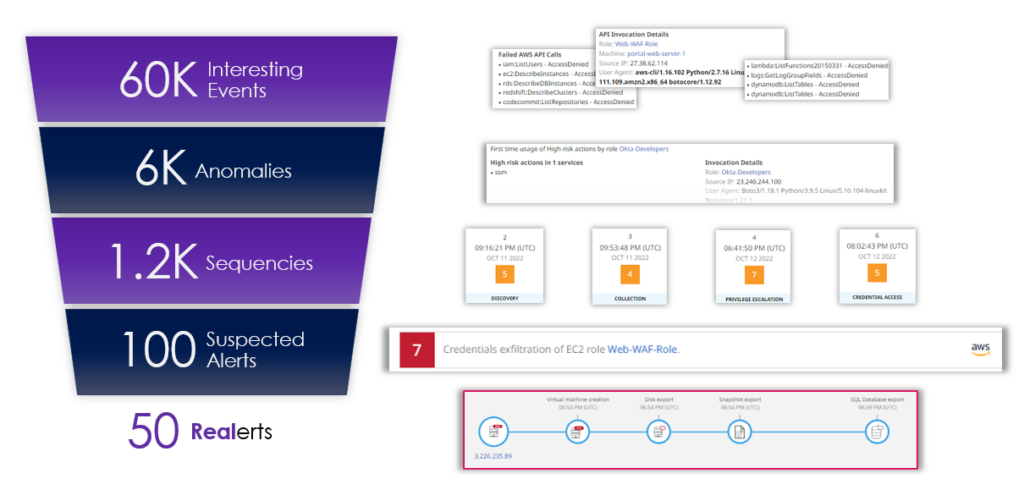
The reason why cloud threat detection is so difficult is for one reason – it requires expertise to make sense of vast amounts of disjointed data and alerts. There is too much data and alerts to sort though, aggregate, correlate, and determine if what is happening is a threat, a one-off, a mistake in employee […]
New Horizons in Cloud Security Part 2: Benchmarking and Novel Self-improving AI Framework for Maliciousness Classification Using Large Language Models
This blog was written by Amir Shachar, Director, AI and Research. As we saw in Part 1 of this blog series, New Horizons in Cloud Security, the new approach to leveraging large language models was outlined. In this blog, we will dive into the technical details. Logs as well as other telemetries (i.e. activity logs, […]
New Horizons in Cloud Security Part 1: Assembling LLMs to Discern Malicious Activities with “Integrated Learning”
This blog was written by Amir Shachar, Director, AI and Research. The digital landscape constantly evolves, increasing complexity to cloud security. In this dynamic environment, it’s becoming more and more challenging to pinpoint and assess the risks associated with cloud incidents, especially when the sequences in question straddle the line between malicious and benign intentions. […]
Unleashing the Power of Multiple AI Layers for Detecting Unknown Cybersecurity Threats
This blog is authored by Amir Shachar, Chief Data Scientist at Skyhawk Security. If you are reading this blog, you are probably wondering how to detect unknown unknowns in the realm of cybersecurity. The very nature of these unknown threats makes them difficult to detect using conventional security measures. However, by leveraging a platform that […]
Skyhawk Synthesis Security Platform mentioned in the 2023 Gartner® Emerging Tech: Security — Cloud Investigation and Response Automation Offers Transformation Opportunities

This post was written by Jennifer Gill, VP Product Marketing at Skyhawk. Skyhawk Security was recently mentioned in Gartner research, “Emerging Tech: Security – Cloud Investigation and Response Automation Offers Transformation Opportunities”, and we think that it really aligns with our vision and strategy. According to the Gartner report, “Cloud investigation and response automation is […]
The Science Behind our Security – Part 2: The Models

This post about models in cybersecurity was written by Jennifer Gill, VP Product Marketing at Skyhawk. In our first blog on the “Science Behind our Security”, we talked about the three pillars: Models, MBIs, and the Attack Sequence. In this blog, we will focus on the machine learning models. These models are a true differentiator […]
“Toxic Combinations” are Inadequate: A Case Study

Posture management has turned into an exercise in prioritization, but this hasn’t made us safer. This post was written by Chen Burshan, CEO of Skyhawk Security If a Tree Falls in the Forest… We all know the adage, “If a tree falls in the forest and nobody is there to hear it, does it make […]