Table of Contents
Watch the Webinar
This blog is based on our joint webinar with AWS. If you prefer to watch the webinar, you can do so here.
The numbers are no longer theoretical. According to the CrowdStrike 2026 Global Threat Report, AI-autonomous attacks increased 89% year-over-year, nearly doubling in a single year. The average attacker breakout time has dropped from roughly an hour to under 30 minutes, and the fastest recorded intrusion completed in just 27 seconds. Meanwhile, the average security team takes approximately six hours to respond to a threat.
That gap – 27 seconds to attack, six hours to respond – is not a technology problem. It is a structural one. And it is the problem that Skyhawk Security was built to solve.
The Alert Overload Crisis Is Real
Before we talk about solutions, it is worth sitting with the scale of the problem for a moment. At a recent AWS re:Invent, a customer approached Skyhawk’s team and mentioned that their CNAPP platform had generated 16 million alerts. Not 16,000. Sixteen million.
Another customer arrived with 500,000 vulnerabilities in their queue. A third had 115,000 CVEs identified across their environment and even after applying AI context from multiple tools, that number only came down to 7,600. Still an unmanageable workload for any security team.
As Jennifer Gill, VP of Marketing at Skyhawk Security, put it during the company’s April 2026 webinar with AWS: “When everything seems critical, it seems like nothing is. You’re really kind of in constant reactive mode.”
This is the reality for most enterprise security teams today. The tools are generating more signal than ever. The problem is that almost none of it is actionable.
Threat Actors Are Already Using AI – And It Is Working
The shift to AI-powered attacks is no longer a future risk. It is happening now, and it is accelerating. Anthropic publicly confirmed in late 2025 that a Chinese state-sponsored threat actor used Claude to execute a large-scale cyber espionage campaign, with AI performing 80–90% of the attack autonomously. Amazon’s own CJ Moses published a blog on the use of AI by threat actors.
What makes AI-powered attacks particularly dangerous is not just their speed, it is their precision. As Nathan Schmidt, Solutions Engineer at Skyhawk, noted during the webinar: “Even what we called script kiddies out there, that would maybe be more nuisance than anything, are also adopting AI. It’s just amplifying every aspect of threat and risk in the environment.”
The adversary has upgraded. The question is whether your defenses have.
Fight AI Attacks with AI-based Security: The Skyhawk Approach
Skyhawk Security’s answer to AI-powered attacks is an AI-powered defense, specifically, a Continuous Autonomous Purple Team that combines the offensive perspective of a red team with the defensive capabilities of a blue team, running continuously and non-disruptively against your actual cloud environment.
The platform operates in two distinct modes that Skyhawk describes as “left of boom” and “right of boom.”
Left of boom: Preemptive Security
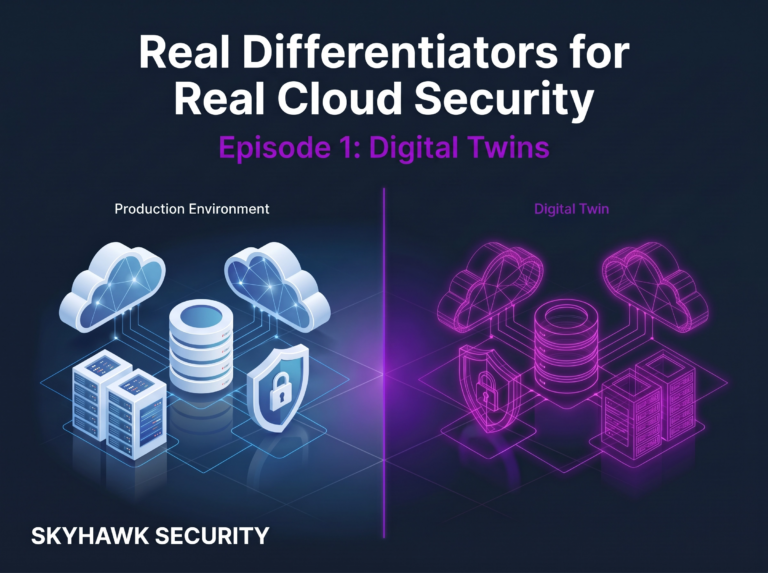
Before an attack occurs, Skyhawk’s Adversarial AI (AI Red Team) continuously simulates attack scenarios against a digital twin of your cloud environment. This is not a scripted library of pre-built attacks. The AI has been trained on thousands of TTPs (tactics, techniques, and procedures) and generates custom attack sequences specific to each customer’s cloud architecture, security controls, IAM configuration, and network topology.
The digital twin is built from read-only metadata collected from the public cloud via a security audit role, no agents, no production impact, no business continuity risk. The AI then manipulates this simulation dynamically, exploring not just what is misconfigured, but what an attacker could actually do with those misconfigurations in combination.
It was demonstrated during the live demo: in one customer environment, the AI identified that a role with excessive permissions could be assumed, an access key retrieved, an EC2 instance created, a custom security group established with its own ingress and egress rules, and remote code execution launched, all in a single, connected attack chain that impacted 43 assets. No existing tool in the customer’s stack had identified this path.
Right of boom: Detection, Response, and SOC Pre-Training
Once attack scenarios are identified, Skyhawk does something that most security tools cannot: it pre-trains the SOC on exactly what those attacks look like. Because the AI has already simulated the attack in the digital twin, the security team has effectively “seen” the attack before it happens in production. This dramatically reduces mean time to resolution – teams are not determining whether an alert is a false positive; they already know what the real attack looks like and how to respond.
Skyhawk also provides automated remediation recommendations, including Terraform scripts for infrastructure-as-code environments, and can generate detection rules for third-party tools like Splunk and others so that responses are coordinated across the entire security stack.
The 1% That Actually Matters
The most striking proof point from the webinar was not a feature – it was a customer result. One customer came to Skyhawk with 500,000 vulnerabilities. After applying the Adversarial AI Red Team, the number of findings that were genuinely weaponizable and connected to crown jewels came down to seven.
Not 50,000. Not 5,000. Seven.
A second customer, working with Tenable data, reduced 41,000 total vulnerabilities down to 114 actionable findings. The customer showcased in the live demo reduced 115,000 CVEs – already filtered through multiple AI-enriched tools – down to a handful of items that genuinely required immediate attention.
This is what Skyhawk calls “finding the 1% that matters.” The platform goes beyond what is theoretically exploitable (which is what CVSS scores and most vulnerability scanners measure) to what is actually weaponizable in your specific cloud environment, meaning an attacker can chain it to other exposures to reach a business-critical asset.
The distinction matters enormously. A high CVSS score on an asset that has no path to a crown jewel is noise. A medium CVSS score on an asset that sits one hop away from your most sensitive data is a crisis. Skyhawk tells you which is which.
Integration with AWS Security Services
Skyhawk is purpose-built for cloud environments and integrates natively with the AWS security ecosystem:
AWS Service | How Skyhawk Uses It |
AWS Inspector | Ingests vulnerability findings and applies Adversarial AI to determine which are actually weaponizable |
Amazon Macie | Uses data classification tags to identify and prioritize crown jewels – assets with sensitive data get elevated priority in attack simulation |
Amazon GuardDuty | Contributes threat detection signals to Skyhawk’s attack sequence analysis and CDR capability |
Skyhawk holds the AWS Security Competency designation, reflecting the depth of this integration and the platform’s alignment with AWS security best practices
Customer Case Studies
Amit Levran, SundaySky: Skyhawk’s Adversarial AI Red Team delivered immediate ROI, reducing alert noise by 99% and surfacing a handful of genuinely critical findings from a queue of hundreds of thousands. In their CNAPP, using the AI Red Team they were able to focus on the top 0.3% of alerts, cutting through 99.7% of the noise to see exactly what was weaponized and what put them at real risk.
Ibex Medical: The team described gaining “a full view of the issues, including the outskirts” – finding exposures they had not previously known existed. They noted becoming proactive with their cloud security for the first time and getting “hours back in their day” that had previously been consumed by alert triage.
Summary
The cloud security challenge in 2026 is not a lack of data. It is a lack of signal. Security teams are buried under alerts generated by tools that were designed to find everything, but not to tell you what actually matters.
AI-powered attackers do not have this problem. They move with precision, speed, and purpose. They identify the weakest path to your most valuable assets and exploit it before your team has finished reading the morning alert queue.
Skyhawk Security fights AI Autonomous Attacks with AI-Powered Cloud Security. Its Continuous Autonomous Purple Team continuously simulates real attack scenarios against your cloud environment, proves which vulnerabilities are genuinely weaponizable, pre-trains your SOC on what real attacks look like, and validates that your security controls will hold when it matters most.
The result is not just fewer alerts. It is genuine, measurable, provable cloud risk reduction.