Recently, at the re:Invent conference, a striking visual at our booth caught the attention of countless attendees. It was a simple depiction of staggering numbers, prompting the same question time and again: “What do those numbers mean?”
Those numbers represent the overwhelming reality for today’s security teams: a torrent of alerts from their Cloud-Native Application Protection Platforms (CNAPPs). One prospect shared a jaw-dropping figure—they were dealing with over 10 million alerts. When everything is an alert, nothing is. This is the critical flaw in many modern cloud security strategies. You aren’t just managing a cloud; you’re navigating a minefield of notifications where the real threats are buried deep beneath the noise.
Your CNAPP is essential for visibility and compliance, but it’s not enough to truly secure your cloud. To cut through the noise and effectively reduce risk, you need to see your environment not as a list of vulnerabilities, but through the eyes of an attacker. You need the adversarial view.
- Alert Fatigue Is No Joke
The sheer volume of alerts generated by CNAPPs is unsustainable. The constant stream of notifications about misconfigurations, vulnerabilities, and potential policy violations creates a state of “alert fatigue,” where security teams become desensitized to the very warnings meant to protect them. This is not just an inconvenience; it’s a significant security risk. When a team is overwhelmed, critical threats are inevitably missed. We spoke to prospects are re:Invent that had millions of critical alerts!
The problem lies in the lack of prioritization and context. A CNAPP might flag thousands of issues, but it often fails to distinguish between a minor, low-risk issue and a critical vulnerability that is part of an active attack chain. To truly secure your cloud, you need a solution that can identify the weaponized threats—the ones that represent a clear and present danger—and provide a clear path to remediation.
Skyhawk Security leverages adversarial emulation to prioritize the critical and high CNAPP alerts by the value of the asset that is at risk for true cloud risk reduction. One of our customers was able to reduce 60,000 alerts to just one that required attention. Learn more here or sign up for a free trial to see this in action.
- You Don’t Need a Static View, You Need an Adversarial View
A typical CNAPP provides a static, siloed view of your cloud security posture. It might identify a year-old, unused permission or a port that has been left open. While these are valid findings, they are merely single data points. They lack the narrative that explains *how* a threat actor could chain these seemingly minor vulnerabilities together to orchestrate a major breach.
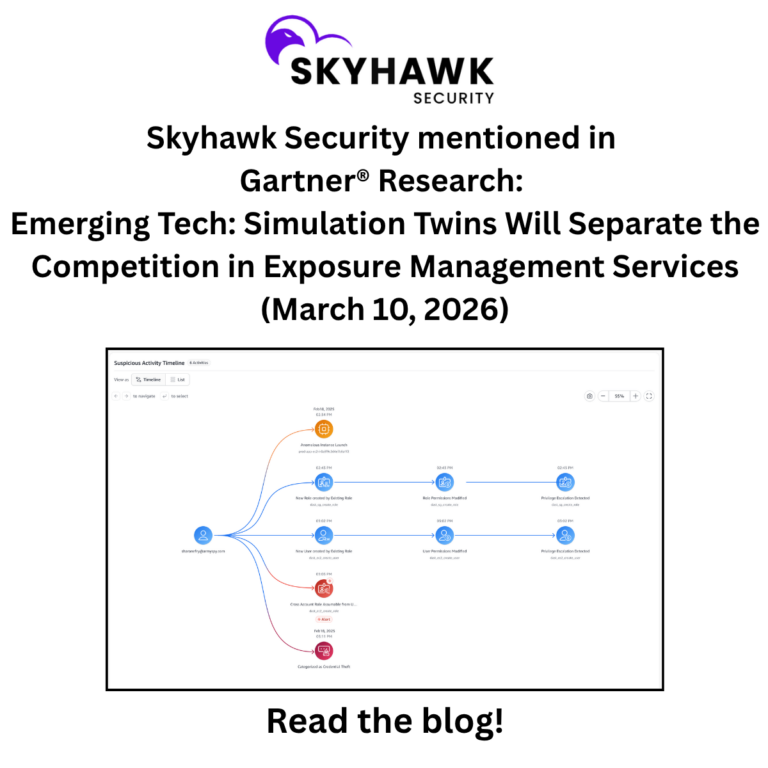
This is where an adversarial perspective, powered by intelligent simulation, becomes a game-changer. Instead of just listing vulnerabilities, Skyhawk Security simulates how a real attacker would operate within your environment. It identifies how a role or identity could be exploited to escalate privileges, move laterally, and ultimately compromise your most valuable assets. This intelligent simulation provides a dynamic, contextualized view of your security weaknesses, allowing you to understand the potential attack paths and prioritize remediation based on the business value of the exposed assets. You’ll know what to fix first because you’ll see exactly how it could be exploited.
- Threat Actors Aren’t Breaking In; They’re Logging In
The modern attack landscape has shifted. The image of a hacker brute-forcing their way into a network is outdated. Today, threat actors are not breaking in; they are logging in. They exploit compromised credentials, misconfigured permissions, and over-privileged identities to gain legitimate access to your cloud environment. Once inside, they operate under the radar, using existing roles and permissions to navigate your systems and access sensitive data.
While traditional scanning and static analysis can help find some of these gaps, they are insufficient on their own. Intelligent simulation, on the other hand, is designed to uncover these identity-based attack paths. It reveals how a compromised identity could be used to escalate privileges and traverse your cloud, giving you the insights needed to lock down these critical pathways before they can be exploited.
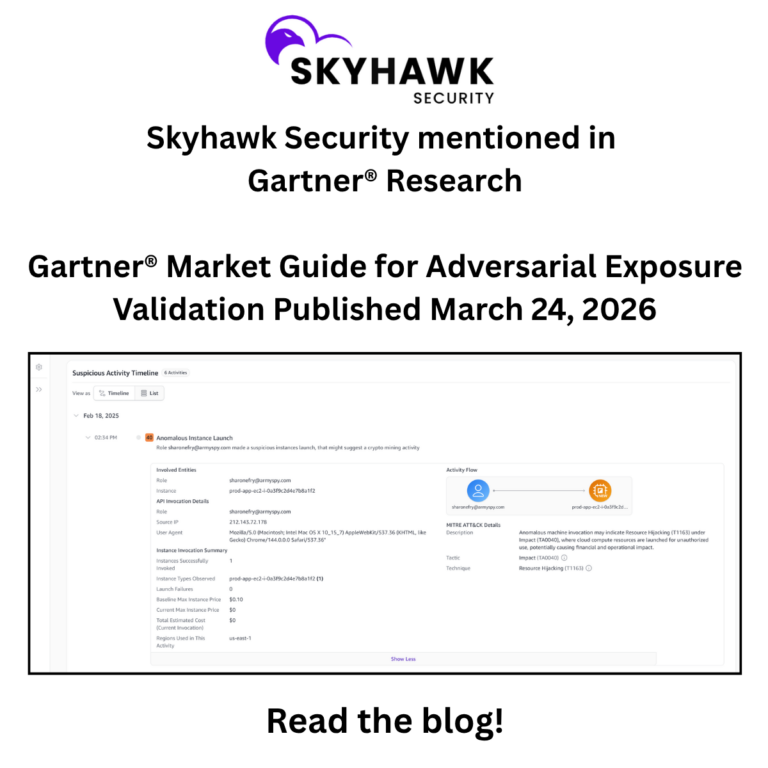
- Real-Time Threat Detection Is Critical
Static scans and periodic assessments can only show you a snapshot in time. The cloud, however, is a dynamic environment, with resources being spun up and down, and permissions changing constantly. To effectively defend against modern threats, you need to be able to detect malicious activity as it happens. Real-time threat detection is critical to finding threats that are happening in your cloud, right now!
Skyhawk Security provides this real-time detection capability, continuously monitoring your cloud environment for anomalous behavior and active threats. By focusing on the tactics, techniques, and procedures (TTPs) used by attackers, it can identify malicious activity that would be missed by traditional security tools. This allows you to respond to threats in real-time, before they can escalate into a full-blown breach.
- Context Matters: The Case of the “Critical” Alert
We heard this story repeatedly at re:Invent. A DevOps team receives a critical alert from their CNAPP and is told to drop everything and fix it immediately. The team scrambles, only to discover that the “critical” vulnerability is in a test environment that is no longer in use. While the issue should eventually be addressed, it poses no immediate threat to the business. For the security team, it was a critical alert that needed to be resolved. For the DevOps team, it was a complete waste of time and a source of significant frustration.
This is a classic example of how a lack of context can undermine security efforts. Without understanding the business context of an asset, it’s impossible to accurately assess its risk. Skyhawk Security enriches security alerts with this crucial business context, allowing you to distinguish between a critical vulnerability in a production environment and a low-risk issue in a development sandbox. This ensures that your teams are focused on the threats that truly matter, eliminating wasted effort and building a more effective security culture.
Complete Your CNAPP with Skyhawk Security
A CNAPP is a powerful tool for gaining visibility into your cloud environment, but it is not a complete security solution. To effectively defend against modern cloud threats, you need to augment your CNAPP with the adversarial perspective and real-time threat detection capabilities of Skyhawk Security.
By providing a weaponized view of threats, simulating attack paths, detecting active threats in real-time, and enriching alerts with business context, Skyhawk Security cuts through the noise of your CNAPP and allows you to focus on what matters most: reducing your cloud risk. Stop drowning in alerts and start seeing your cloud through the eyes of an attacker. It’s time to complete your cloud security picture.