Table of Contents
This blog leverages data from Crowdstrike’s 2026 Global Threat Report.
The CrowdStrike 2026 Global Threat Report is one of the most important threat intelligence documents published each year. This year’s edition carries a clear and urgent message: adversaries have fundamentally changed how they operate, and most security programs have not kept pace.
At Skyhawk Security, we read this report carefully. Not because the findings surprised us, they validated everything we have been building toward, but because the data is now impossible to ignore. The threat is faster, stealthier, and more automated than ever before. The defenses organizations rely on were designed for a different era.
Below are the ten most important cloud security takeaways from the CrowdStrike 2026 report, and what each one means for how organizations need to defend themselves going forward.
The Attacker Timeline Has Collapsed and Human-Speed Defense Cannot Keep Up
The average eCrime breakout time in 2025 fell to 29 minutes, down 65 percent from the prior year. The fastest observed breakout took just 27 seconds. In one documented intrusion, data exfiltration began within four minutes of initial access.
These numbers represent a fundamental shift in what defense actually requires. When an attacker can move from initial foothold to lateral movement to data exfiltration in under half an hour, any security workflow that depends on a human reviewing and then triaging an alert, escalating a ticket, and making a decision is already too slow.
This is the core argument for autonomous security. The window to detect and contain an intrusion is now measured in seconds and minutes, not hours. Security platforms must be able to identify threat activity and respond at machine speed, without waiting for human intervention at every step.
Malware Is No Longer the Primary Attack Vector, Legitimate Tools Are
In 2025, 82 percent of all detections were malware-free, up from 51 percent in 2020. Attackers are not breaking in. They are logging in, using legitimate credentials, native operating system tools, and approved administrative functions to move through environments without triggering traditional detection controls.
This trend exposes a critical gap in most security architectures. Signature-based detection, antivirus, and traditional endpoint tools are designed to identify malicious code. When there is no malicious code, when the attacker looks exactly like a legitimate user, those tools generate no alerts.
The implication is that behavioral analysis, identity monitoring, and contextual correlation are no longer optional. They are the primary mechanism through which modern threats must be detected.
Skyhawk’s detection models are built around behavioral anomalies correlated with business context, not signatures. The platform identifies when legitimate access is being used in ways that indicate compromise, even when no malware is present.
Your Cloud Is Now the Primary Target, Not a Secondary One
Cloud-conscious intrusions rose 37 percent year-over-year in 2025. Among named state-nexus threat actors are Russia, China, Iran, and North Korea, the increase was 266 percent. These are not opportunistic attacks. They represent sustained, strategic investment in cloud-targeting capabilities by the most sophisticated adversaries in the world.
The implication for security teams is significant. Cloud environments can no longer be treated as an extension of the on-premises perimeter. They are the primary target, and they require security platforms that were designed for the cloud from the ground up, not legacy tools retrofitted for cloud deployments.
Skyhawk was built cloud-native from the beginning. Every capability, from threat simulation to real-time detection to autonomous response, was designed specifically for the dynamics of cloud environments, including multi-cloud architectures, ephemeral workloads, and cloud-native identity systems.
Valid Account Abuse Is the Defining Technique of Cloud Intrusions
Of all cloud incidents in 2025, 35 percent involved the abuse of valid accounts. Attackers obtained legitimate credentials through phishing, vishing, social engineering, and credential theft, then used those credentials to move through cloud environments in ways that appeared entirely normal.
SCATTERED SPIDER, one of the most active and disruptive adversaries tracked in the report, gained full domain controller access within three hours using only one managed endpoint interaction. The rest of the intrusion was conducted through legitimate credentials and trusted administrative tools.
This is the identity security challenge in its most concrete form. When an attacker has valid credentials, they do not look like an attacker. They look like a user doing their job. Traditional perimeter security and even many identity tools are not equipped to distinguish between legitimate access and attacker-controlled access when the credentials are real.
Skyhawk addresses this directly by continuously analyzing which identities and access paths are weaponizable before an attacker discovers and exploits them. The platform maps credential exposure and permission risk across the environment, identifying the paths that represent the greatest danger if compromised.
Attackers Win by Moving Between Your Tools, Not Through Them
The most disruptive intrusions documented in the 2026 report succeeded not by defeating any single security control, but by exploiting the gaps between controls. BLOCKADE SPIDER used a compromised SSO account to modify EDR policies, effectively creating an unmonitored staging directory for malicious activity. SCATTERED SPIDER moved across endpoints, cloud environments, identity systems, and SaaS applications within a single campaign.
The report is explicit on this point: organizations that monitor each surface individually like endpoint, cloud, identity, SaaS face fragmented responses and missed threats. The responsibility for triaging alerts across different platforms is distributed across different teams, and the connections between events are lost in the handoff.
CrowdStrike’s own recommendation is to eliminate cross-domain blind spots by consolidating telemetry and applying cross-domain correlation through XDR and SIEM workflows.
Skyhawk operates across the full security stack. The platform ingests and correlates signals from SIEMs, CNAPPs, CloudWatch, and other tools, identifying the attack paths that span multiple domains and surfaces. The gaps between your tools are where Skyhawk looks first.
AI Has Permanently Changed the Attacker Capability Curve
AI-enabled adversary operations increased by 89% year-over-year in 2025. Threat actors of every skill level are now using commercial AI tools such as ChatGPT, Gemini, DeepSeek, and others to accelerate reconnaissance, generate phishing content, write malware, and execute post-exploitation activities.
Critically, the report notes that AI is not creating fundamentally new attack vectors. It is dramatically accelerating and scaling existing ones. Less sophisticated actors can now execute attacks that previously required advanced technical expertise. More sophisticated actors can operate at speeds and scales previously unattainable.
FANCY BEAR deployed a novel malware family called LAMEHUG that embedded an LLM directly into the malware to perform reconnaissance and intelligence collection. PUNK SPIDER used AI-generated scripts to execute credential dumping and destroy forensic evidence. The integration of AI into attacker operations is no longer theoretical. It is operational.
The only effective response is to fight AI with AI. Skyhawk’s adversarial AI continuously simulates how an attacker would move through your specific environment, identifying the paths that are most likely to be exploited. The platform does not simulate generic attack patterns. It models the actual risks present in your architecture.
Proactive Security Is No Longer Optional. It Is the Prerequisite.
One of the clearest themes in the CrowdStrike 2026 report is that reactive defense has become insufficient. When breakout times are measured in seconds, and when attackers move through legitimate access paths that generate no alerts, the only way to stop breaches is to identify and close attack paths before the adversary arrives.
CrowdStrike’s recommendations explicitly call for prioritizing proactive threat intelligence and hunting, and for augmenting analysts with specialized AI agents that can operate at the speed and scale required.
This is the concept Skyhawk calls Left of Boom. Acting before the attack happens, rather than responding after it has already succeeded. Skyhawk’s continuous adversarial AI simulation models how an attacker would target your environment right now, given your current configuration, your current identity exposure, and your current security stack. It finds what is weaponizable before the attacker does.
The alternative is to wait for an alert that may arrive 27 seconds too late.
Identity and Hybrid Identity Systems Are the New Perimeter
The 2026 report documents a significant and deliberate shift by both eCrime and nation-state adversaries toward targeting hybrid identity systems, the technologies that bridge on-premises Active Directory with cloud-based identity platforms like Microsoft Entra ID.
SCATTERED SPIDER and BLOCKADE SPIDER both targeted Entra Connect Sync and Active Directory Federation Services to gain privileged access across cloud and on-premises environments simultaneously. MURKY PANDA specialized in abusing trusted relationship connections between Entra ID tenants to compromise downstream organizations. COZY BEAR combined OAuth 2.0 phishing with multi-channel social engineering to compromise accounts without ever touching a suspicious domain.
The common thread is that identity infrastructure is now the primary attack surface for the most sophisticated adversaries in the world. Compromising identity systems provide access that spans the entire environment: endpoints, cloud workloads, SaaS applications, and data stores.
Skyhawk’s capabilities continuously analyze identity permissions and access configurations, identifying overprivileged accounts, exposed credentials, and misconfigured trust relationships before they can be exploited. The platform treats identity security as a first-class concern, not an afterthought.
Alert Volume Is Not a Security Program, Prioritization Is
The scale of the detection challenge facing modern security teams is difficult to overstate. A typical enterprise environment can generate hundreds of thousands of raw findings per month: vulnerabilities, misconfigurations, behavioral alerts, threat intelligence matches. Without a way to prioritize that volume, security teams are effectively paralyzed by noise.
The 2026 report underscores this problem by documenting how attackers move through environments in ways that generate little or no alert activity. The signal that matters is buried under an enormous volume of signals that do not.
Skyhawk addresses this by reducing 500,000 raw findings per month to approximately 300 actionable risks, a noise reduction of 99.9 percent. This is not achieved by ignoring alerts. It is achieved through Skyhawk’s Adversarial AI by validating which findings represent genuinely weaponizable risks in your specific environment, and prioritizing them based on the business value of the assets at risk.
The goal is not to find more problems. It is to find the right problems, the ones that an attacker would actually exploit, in the order that matters most to your organization.
The Security Stack You Have Is Only as Good as Your Ability to Validate It
The final and perhaps most important takeaway from the 2026 report is one that is easy to overlook: having security tools is not the same as having a validated security posture. The intrusions documented throughout the report succeeded in environments that had EDR, SIEM, identity tools, and cloud security controls in place. Those controls were bypassed, misconfigured, or simply not connected to each other in ways that would have caught the attack.
BLOCKADE SPIDER modified an existing EDR exclusion rule to apply to all users, creating an unmonitored staging directory. SCATTERED SPIDER moved through cloud and identity infrastructure while interacting with only one managed endpoint. The tools were present. The gaps between them were not visible.
CrowdStrike’s recommendation is explicit: organizations need to validate their defenses continuously, not just deploy them. This means regular tabletop exercises, red and blue team operations, and proactive hunting for the gaps that adversaries will find if defenders do not find them first.
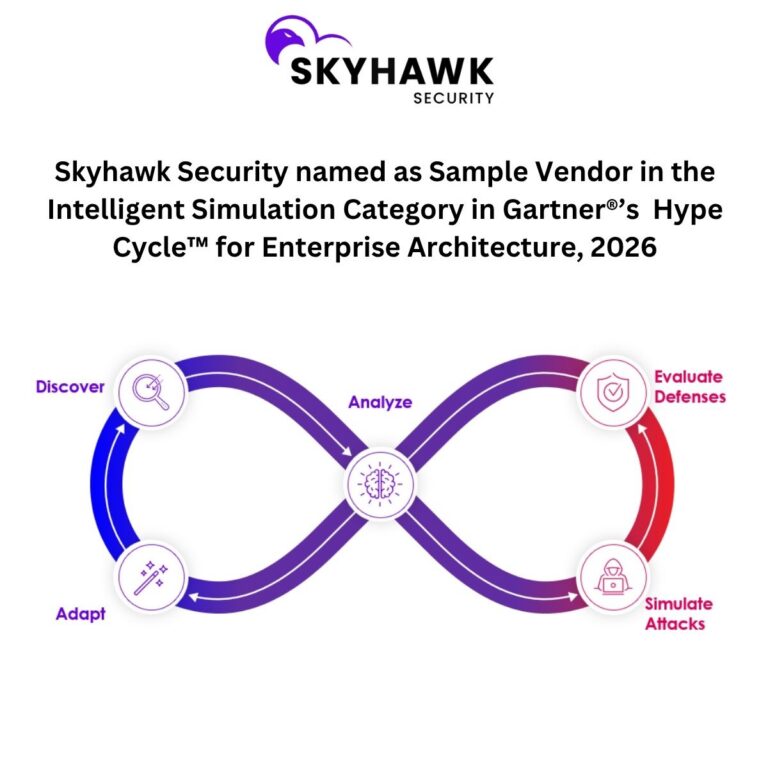
Skyhawk’s Intelligent Simulation capability does exactly this. The platform validates your actual security stack like SIEM, EDR, WAF, CloudWatch, and more against real threat scenarios tailored to your environment. It does not test against generic scripts. It identifies whether your controls would actually detect and stop an attacker moving through your specific architecture.
The CrowdStrike 2026 report tells you what the threat looks like. Skyhawk tells you whether you are actually prepared for it.
The Bottom Line
The CrowdStrike 2026 Global Threat Report is a detailed and evidence-based account of how the threat landscape has changed. The attackers are faster, they are using AI, they are operating through legitimate credentials and trusted systems, and they are winning by moving between the gaps in fragmented security architectures.
The report’s recommendations align precisely with what Skyhawk was built to deliver: continuous adversarial simulation, autonomous AI-powered response, cross-domain visibility, identity and permission hardening, and the ability to validate whether your security stack will actually hold when an attacker arrives.
The question is not whether your organization will be targeted. The question is whether you will see the attacker coming before they reach what matters most.
To see your cloud through an adversary’s eyes, schedule a demo with Skyhawk Security at skyhawk.security.